An ongoing phishing operation has been identified as targeting a diverse range of organizations since April 2025. The campaign utilizes Remote Monitoring and Management (RMM) software to maintain stealthy access to compromised systems, cybersecurity experts revealed.
Dubbed VENOMOUS#HELPER by Securonix, this campaign has affected over 80 organizations, primarily within the United States. It shares characteristics with previously documented clusters by Red Canary and Sophos, the latter referring to it as STAC6405. Although the perpetrators remain unidentified, the tactics suggest involvement by financially motivated Initial Access Brokers or ransomware actors.
Exploiting Legitimate Software for Access
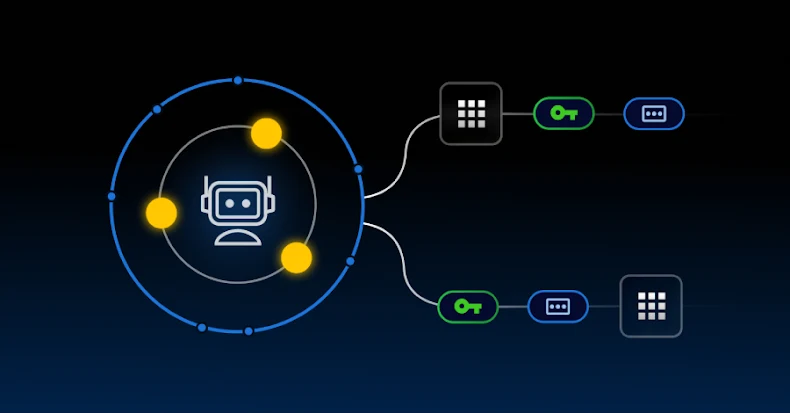
The attackers employ customized versions of SimpleHelp and ScreenConnect RMM tools to circumvent security measures, leveraging their legitimate appearance to deceive targets. This strategy aims to construct a dual-channel access system, ensuring continuous operation even if one channel is shut down.
The attack commences with phishing emails masquerading as communications from the U.S. Social Security Administration (SSA), urging recipients to verify their email and download an SSA statement via a link. This link directs users to a compromised Mexican business website, gruta.com.mx, to bypass spam filters.
Technical Execution and Persistence
Once the SSA statement is ‘downloaded’ from another attacker-controlled domain, it delivers the SimpleHelp RMM tool through a seemingly innocuous executable. This executable installs itself as a Windows service, persistently maintaining operation by employing a watchdog mechanism that restarts the malware if terminated.
The SimpleHelp client escalates privileges using SeDebugPrivilege, and a legitimate executable, elev_win.exe, to attain SYSTEM-level access. This allows the threat actor to monitor desktops, inject keystrokes, and interact with user resources. Should the SimpleHelp channel be disrupted, ConnectWise ScreenConnect serves as an alternative communication path.
Implications for Security and Future Outlook
The SimpleHelp version 5.0.1 deployed in these attacks provides extensive remote administration capabilities, leaving victim organizations vulnerable to ongoing exploitation. Attackers can execute commands, transfer files, and infiltrate adjacent systems, all while evading detection due to the software’s legitimate signatures.
This campaign highlights the challenges faced by security teams in detecting and mitigating threats that misuse authentic tools. Organizations must enhance their defensive strategies and remain vigilant against such sophisticated attacks.