TeamPCP Targets Checkmarx GitHub Actions
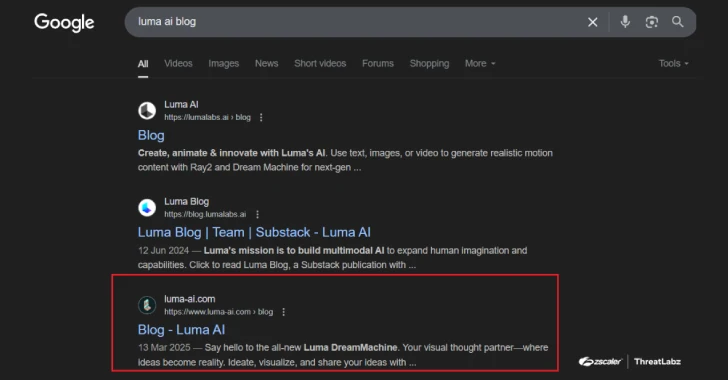
TeamPCP, a notorious cybercriminal group, has recently compromised two GitHub Actions workflows maintained by Checkmarx, utilizing malware to steal credentials. This incident follows their previous attack on Trivy, a supply chain security tool, suggesting a broader campaign by the group.
Details of the Credential Theft
According to cloud security experts at Sysdig, the same malware used against Trivy has now targeted Checkmarx. The breach, which surfaced in March 2026, allowed attackers to extract sensitive data, tracked under CVE-2026-33634 with a high severity score of 9.4.
The malware, known as the “TeamPCP Cloud stealer,” is engineered to extract credentials and secrets from various cloud services, databases, and communication platforms. This includes data from Amazon Web Services, Google Cloud, and Microsoft Azure, among others.
Attack Methodology and Impact
The attackers employed a technique involving force-pushing tags to insert malicious scripts into the workflows. They also devised a backup method to store stolen data on GitHub, using repository names like “docs-tpcp,” to ensure data retrieval even if direct exfiltration failed.
Sysdig highlighted that the attackers used vendor-specific domains to mask their activities, reducing detection chances. This breach potentially enables further supply chain attacks by compromising additional repositories.
Mitigation and Response Strategies
Security experts recommend immediate actions to mitigate the threat. These include rotating all compromised credentials, auditing workflow logs for suspicious activity, and securing GitHub Actions by pinning them to full commit SHAs.
Additionally, monitoring network traffic from CI runners and restricting certain metadata services can help prevent further breaches. The attack on Checkmarx is part of a larger pattern by TeamPCP to escalate their operational reach.
In response to this threat, organizations must implement stringent security measures to protect their CI/CD environments and cloud platforms, ensuring that similar attacks do not compromise their supply chains.