A previously unreported cyber threat group, UNC6692, is utilizing social engineering techniques through Microsoft Teams to deploy a sophisticated malware suite on compromised systems. According to a report by Mandiant, a Google subsidiary, UNC6692 is masquerading as IT helpdesk staff to trick victims into accepting chat invitations from external accounts.
Impersonation and Social Engineering Tactics
UNC6692 is linked to extensive email campaigns designed to inundate targets with spam, creating a false urgency. Once the target’s inbox is overwhelmed, the attackers approach them via Microsoft Teams, posing as IT support to offer assistance with the email flood. This strategy mirrors tactics previously used by Black Basta affiliates, despite their cessation of ransomware operations last year.
ReliaQuest, in a recent report, highlighted how these attacks primarily aim at executive and senior staff, seeking initial access to corporate networks for data theft and potential ransomware deployment. Often, attackers initiate chat conversations rapidly, sometimes with merely 29 seconds between them, to maintain the illusion of urgency.
Deployment of Remote Monitoring Tools
The attackers’ objective is to deceive victims into installing legitimate remote monitoring and management (RMM) tools, such as Quick Assist or Supremo Remote Desktop. These tools provide attackers with direct access, allowing them to install additional malicious payloads.
Between March 1 and April 1, 2026, incidents targeting senior employees surged to 77%, a significant increase from the previous two months. This demonstrates the enduring effectiveness of these tactics, as noted by ReliaQuest researchers John Dilgen and Alexa Feminella.
Malware Distribution and Phishing Techniques
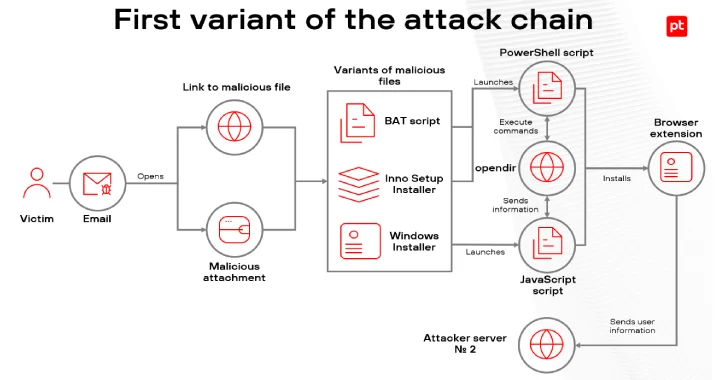
Mandiant’s report details a variation in attack methods where victims click on a phishing link in a Teams chat, purportedly to install a local patch. This link directs to an AutoHotkey script download from an attacker-controlled AWS S3 bucket. The phishing page, labeled “Mailbox Repair and Sync Utility v2.1.5,” initiates reconnaissance and installs SNOWBELT, a malicious browser extension, on Microsoft’s Edge browser.
This extension facilitates further malware deployment, including SNOWGLAZE and SNOWBASIN, which are integral to the SNOW malware ecosystem. These components enable command execution, create secure tunnels for data exfiltration, and maintain persistent backdoor access.
Implications and Future Outlook
The UNC6692 campaign underscores a sophisticated evolution in cyberattack strategies, blending social engineering with custom malware. By exploiting trusted cloud services for malware delivery and control, attackers effectively bypass traditional security measures.
As similar tactics continue to emerge, such as those involving voice phishing and trojan deployment via Microsoft Teams, organizations must prioritize enhancing security measures around collaboration tools. This includes enforcing verification workflows and tightening controls to safeguard against these evolving threats.