QNAP has launched a safety advisory detailing a vulnerability in its NetBak Replicator utility that might enable native attackers to execute unauthorized code.
The flaw, recognized as CVE-2025-57714, has been rated as “Essential” and impacts particular variations of the backup and restore software program. The corporate has already issued a patch and is urging customers to replace their programs to forestall potential exploitation.
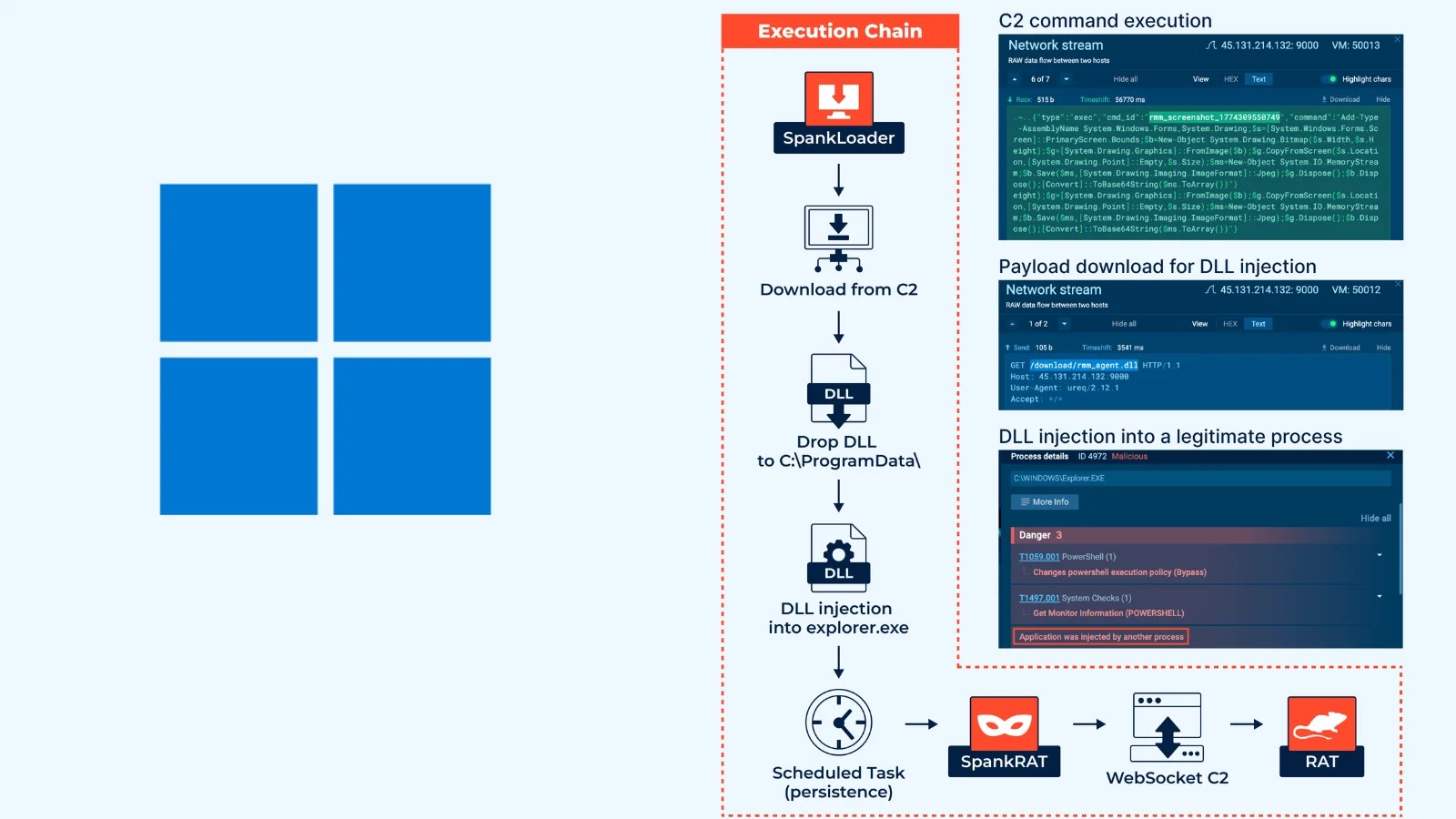
This vulnerability stems from an unquoted search path or ingredient throughout the NetBak Replicator software program. Any such flaw happens when the trail to an executable file is just not correctly enclosed in citation marks.
If a neighborhood attacker has already gained entry to a consumer account on the system, they will place a malicious executable in a mum or dad listing of the legit program’s path.
The working system might then inadvertently execute the malicious file as an alternative of the meant one, resulting in unauthorized code execution with the permissions of the operating software.
Affected Merchandise
The vulnerability particularly impacts NetBak Replicator variations 4.5.x. Based on the advisory launched on October 4, 2025, a profitable exploit requires an attacker to have prior entry to a neighborhood consumer account.
From there, they will leverage the unquoted search path to execute arbitrary instructions or code. This might enable the attacker to escalate privileges, set up persistent malware, or manipulate knowledge on the compromised system.
Whereas the assault requires native entry, it represents a major danger in multi-user environments or as a post-exploitation method for privilege escalation.
CVE IDAffected Product(s)ImpactPrerequisitesCVSS 3.1 ScoreCVE-2025-57714NetBak Replicator 4.5.xUnauthorized code executionLocal attacker with consumer account accessNot Publicly Disclosed
Mitigations
QNAP has addressed the safety flaw in NetBak Replicator model 4.5.15.0807 and all subsequent releases.
The corporate strongly recommends that every one customers of the affected software program variations replace to the newest patched model instantly to guard their gadgets from potential assaults.
Customers can discover the newest software program updates by visiting the official QNAP Utilities webpage. Usually updating software program is a important safety apply that ensures programs are protected in opposition to newly found vulnerabilities and threats. The invention of this vulnerability was credited to Kazuma Matsumoto of GMO Cybersecurity by IERAE, Inc.
Observe us on Google Information, LinkedIn, and X for each day cybersecurity updates. Contact us to characteristic your tales.