A current phishing marketing campaign is abusing QR codes in a brand new manner, turning easy HTML tables into working codes that redirect customers to malicious websites.
As an alternative of embedding a QR picture within the e-mail physique, the attackers construct the code from a whole bunch of tiny desk cells, every styled as black or white.
The end result nonetheless scans like a traditional QR code, however many e-mail defenses fail to deal with it as a picture.
The messages, seen between December 22 and December 26, comply with a minimal design: a brief lure textual content and a single “squished” QR code block that urges the sufferer to scan it.
Every QR code redirects to subdomains of lidoustoo[.]click on, usually utilizing the recipient’s personal area identify within the URL path to look extra convincing, resembling hxxps[:]///. This construction helps the hyperlink seem much less suspicious at a look.
Web Storm Heart researchers famous that the QR itself is rendered purely by way of HTML, utilizing a desk product of 4×4 pixel cells with black and white background colours.
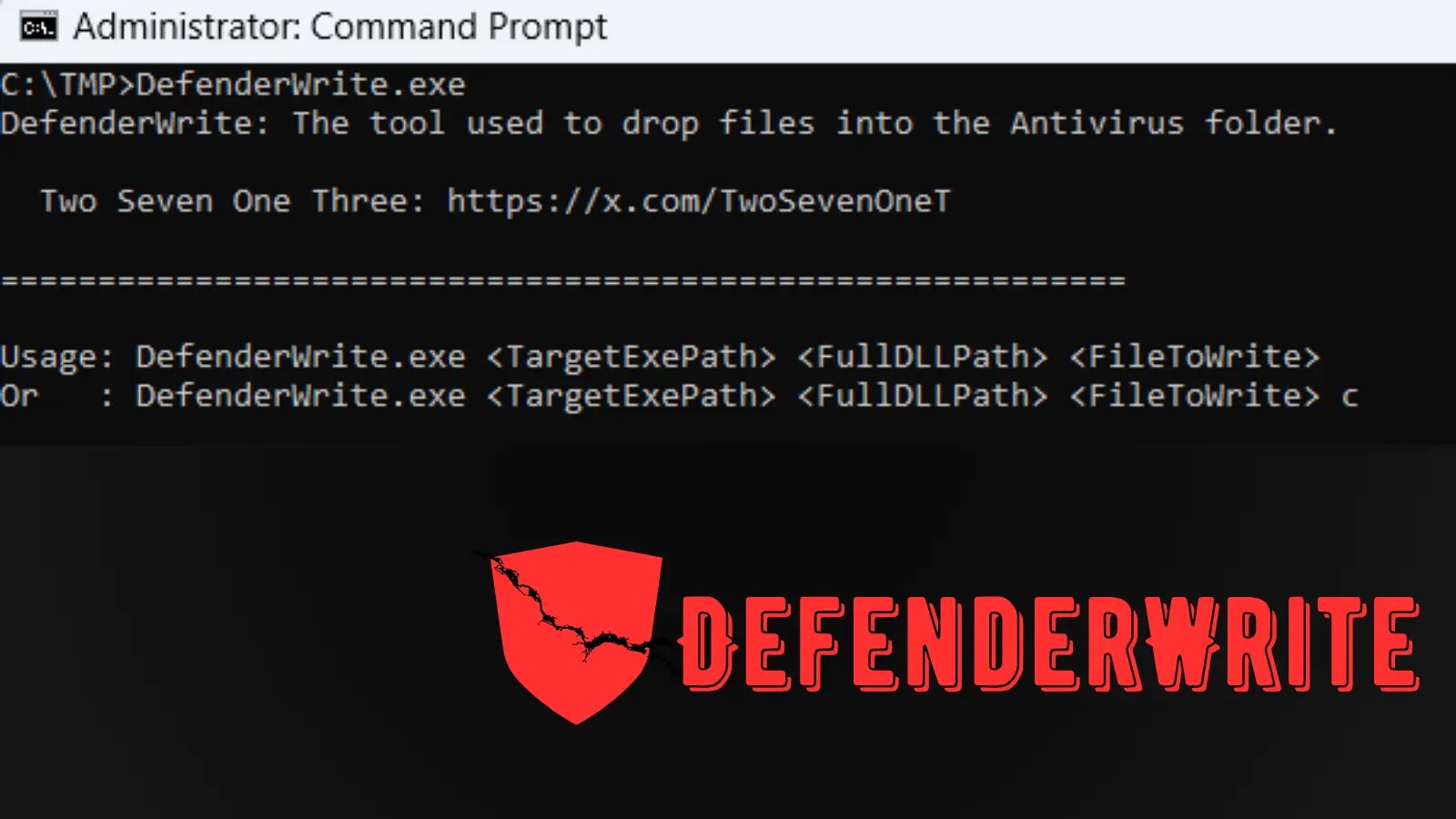
Malicious Imageless QR Code (Supply – Web Storm Heart)
This method bypasses many QR inspection engines, that are tuned to scan precise picture attachments or inline picture information. The e-mail HTML, nonetheless, seems like innocent structure markup to easy content material filters.
In a single captured pattern, the QR is created utilizing code just like the snippet under, which defines a dense matrix of cells to encode the sample:
Detection Evasion By HTML Desk-Primarily based QR Codes
This imageless QR method exploits a blind spot in lots of safe e-mail gateways.
Instruments that may decode QR photographs don’t at all times examine HTML tables as potential graphical buildings, so the malicious sample slips previous QR-focused checks.
On the similar time, content material filters see solely customary tags and shade attributes, not apparent phishing key phrases or picture hashes.
For defenders, the marketing campaign is a reminder that protections can not rely solely on how threats “often” look. Safe e-mail filters should deal with dense desk grids as doable QR renderings, apply DOM-aware evaluation, and flag uncommon exterior redirects.
In parallel, customers ought to be educated that scanning QR codes from unsolicited emails is as dangerous as clicking unknown hyperlinks, even when the code seems easy and clear.
Observe us on Google Information, LinkedIn, and X to Get Extra Instantaneous Updates, Set CSN as a Most well-liked Supply in Google.