The ShinyHunters risk group has expanded its extortion operations with subtle assault strategies focusing on cloud-based techniques throughout a number of organizations.
These cybercriminals use voice phishing and pretend credential harvesting web sites to steal login data from workers.
As soon as they acquire entry, they extract delicate knowledge from cloud software program functions and use this data to demand ransom funds from sufferer firms.
The risk group creates realistic-looking phishing web sites that mimic firm login pages to seize single sign-on credentials and multi-factor authentication codes from unsuspecting workers.
The attackers usually name workers whereas pretending to be IT employees members and declare the corporate is updating safety settings. They then direct staff to fraudulent web sites designed to steal their login credentials.
This method has confirmed efficient as a result of it combines human manipulation with technical deception.
Google Cloud analysts recognized that the risk exercise is being tracked beneath three separate risk clusters named UNC6661, UNC6671, and UNC6240.
The researchers found that these teams have expanded the quantity and forms of cloud platforms they aim, searching for extra helpful knowledge for his or her extortion schemes.
Current incidents present the attackers are utilizing aggressive techniques together with harassment of sufferer workers and launching denial-of-service assaults towards firm web sites.
Assault path diagram (Supply – Google Cloud)
The assaults don’t exploit safety vulnerabilities in software program merchandise or infrastructure. As a substitute, they succeed via social engineering methods that trick folks into offering their credentials voluntarily.
Safety consultants emphasize that organizations ought to undertake phishing-resistant authentication strategies similar to FIDO2 safety keys or passkeys, which can’t be bypassed via social engineering techniques like conventional SMS or push-based authentication techniques.
Assault Mechanism and Information Theft Operations
The risk actors register faux domains that impersonate reputable company portals utilizing patterns like companynamesso.com or companynameinternal.com to make their phishing websites seem genuine.
After acquiring worker credentials, the attackers register their very own authentication units to keep up persistent entry to sufferer accounts.
They then systematically transfer via company cloud environments to steal knowledge from platforms together with SharePoint, Salesforce, DocuSign, and Slack.
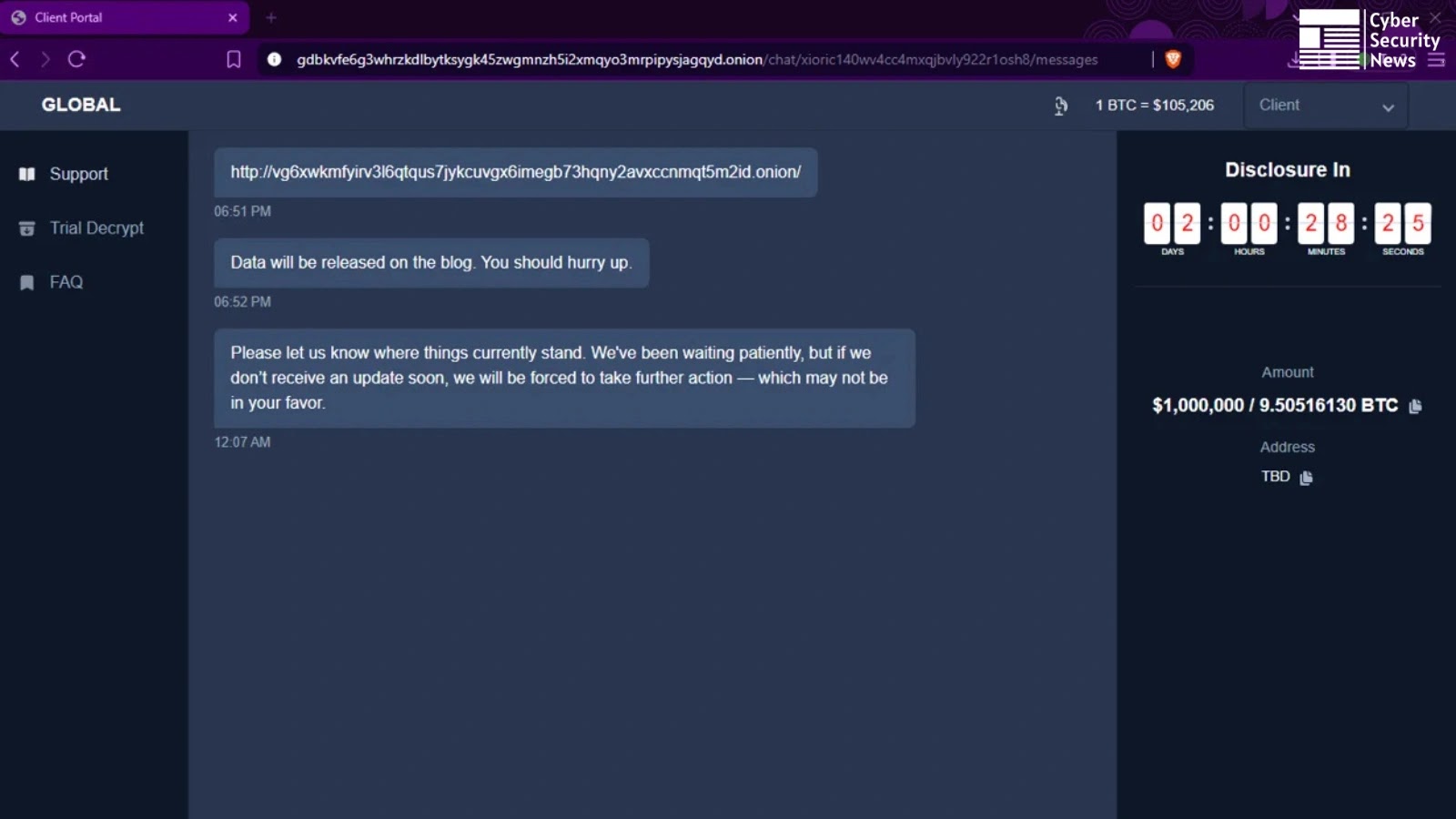
Ransom observe (Supply – Google Cloud)
The cybercriminals search particularly for paperwork containing phrases like “confidential,” “inner,” “proposal,” and “vpn” inside cloud functions.
In some instances, they enabled particular instruments like ToogleBox Recall inside Google Workspace accounts to completely delete safety notification emails, stopping workers from discovering that unauthorized units have been accessing their accounts.
After stealing knowledge, the attackers ship extortion emails demanding Bitcoin funds inside 72 hours and supply samples of stolen data hosted on file-sharing platforms to show their claims.
Comply with us on Google Information, LinkedIn, and X to Get Extra On the spot Updates, Set CSN as a Most well-liked Supply in Google.