A recent surge in phishing activities is targeting Spanish-speaking users across organizations in Latin America and Europe. The campaign employs dynamic PDF documents to distribute banking trojans, notably Casbaneiro, also known as Metamorfo. This is achieved through another malware, Horabot, as part of a complex attack strategy by a Brazilian cybercrime group identified as Augmented Marauder and Water Saci, first reported by Trend Micro in October 2025.
Phishing Tactics and Techniques
Security researchers from BlueVoyant, Thomas Elkins and Joshua Green, revealed in a recent analysis that the group’s methods include the use of WhatsApp, ClickFix techniques, and email-centric phishing. These tactics aim to compromise both consumer and enterprise users by leveraging automated scripts and an advanced email-hijacking system.
The phishing attacks begin with emails that mimic court summons, tricking recipients into opening password-protected PDF attachments. These PDFs contain links that lead to malicious downloads, triggering the execution of harmful scripts and payloads. The VBS script, a part of this sequence, conducts checks for security software like Avast before retrieving further malicious files from remote servers.
Unfolding the Attack Chain
Among the downloaded elements are loaders that execute encrypted files, eventually deploying the Casbaneiro and Horabot malware. Casbaneiro, the primary threat, communicates with command-and-control servers, fetching scripts to further spread the malware via phishing emails through compromised Microsoft Outlook accounts.
Horabot facilitates this propagation, creating dynamic PDFs that impersonate official documents. This malware also includes a secondary DLL, targeting major email services such as Yahoo, Live, and Gmail to hijack accounts and send phishing emails.
Continued Evolution of Cyber Threats
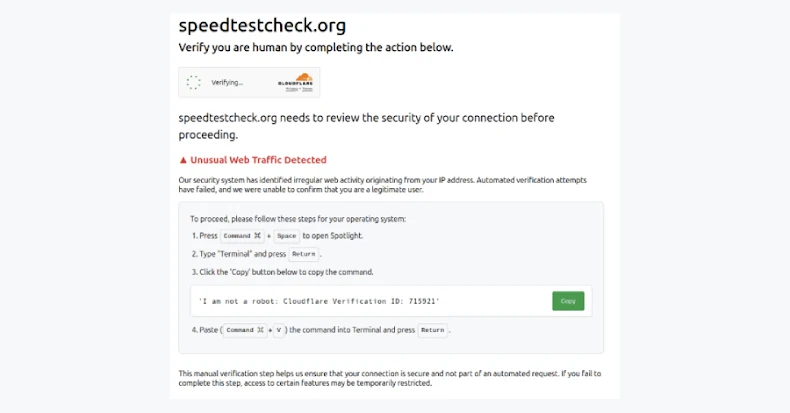
Water Saci’s history of using WhatsApp as a vector for banking trojans like Maverick and Casbaneiro demonstrates their adaptive strategies. Recent campaigns highlighted by Kaspersky have utilized the ClickFix tactic to deploy malicious files, underscoring the evolving nature of these threats.
The integration of social engineering with dynamic PDF generation and automated WhatsApp tactics reflects an increasingly sophisticated adversary, capable of circumventing advanced security measures. This multifaceted attack strategy, combining multiple channels like WhatsApp and email with dynamic, user-specific lures, presents a significant challenge to cybersecurity defenses.
As these threats continue to advance, organizations must remain vigilant and adopt robust security measures to protect against such innovative and persistent cybercriminal activities.