Recent investigations by cybersecurity experts have unearthed sophisticated cyber attacks originating from North Korea, employing AI-generated npm malware and fake companies to compromise systems. This campaign, dubbed PromptMink, is attributed to the infamous North Korean group, Famous Chollima, also known for the Contagious Interview and IT Worker scams.
AI-Powered npm Malware
The npm package in question, ‘@validate-sdk/v2’, masquerades as a tool for secure development but is designed to extract sensitive information from victim environments. The package shows signs of AI involvement, evident from its generative coding style. Originally uploaded in October 2025, this package is part of a broader scheme involving various npm dependencies.
ReversingLabs, who identified the campaign, notes that the malware’s introduction occurred in a February 2026 commit linked to a Solana blockchain-related project. This package, ‘@solana-launchpad/sdk’, is part of a network of dependencies that collectively enable unauthorized access to cryptocurrency wallets.
Complex Attack Strategies
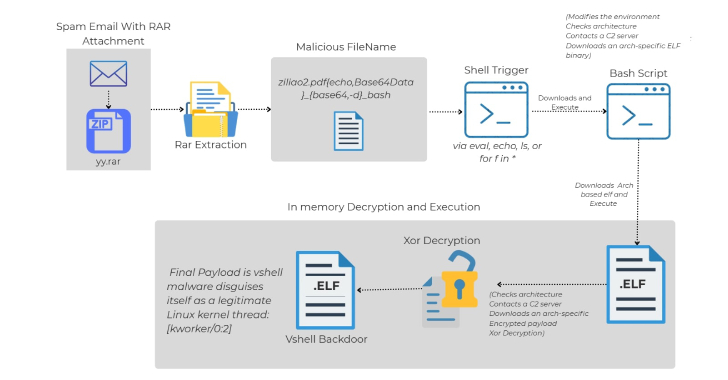
The attack strategy involves multiple layers, where initial packages appear benign while second-layer packages carry malicious code. These secondary packages are swiftly replaced if detected, ensuring continued operation. First-layer packages like ‘@meme-sdk/trade’ and ‘@solmasterv3/solana-metadata-sdk’ are widely used, aiding in the malware’s stealth.
Techniques such as typosquatting and creating malicious versions of popular functions are employed to evade detection. The campaign’s evolution includes targeting Python’s PyPI with similar tactics, leveraging remote access tools, and exfiltrating data from compromised systems.
Broader Implications and Future Outlook
The ongoing threat from DPRK-aligned hackers underscores the vulnerabilities in the open-source ecosystem. With tactics such as social engineering and creating fake companies, these actors continue to exploit developers’ trust in npm and PyPI repositories. Recent efforts include the creation of fake job offers and utilizing GitHub-hosted malicious dependencies.
As these attacks evolve, cybersecurity experts emphasize the need for enhanced vigilance and improved detection mechanisms to protect against such sophisticated threats. Organizations and developers in the cryptocurrency and blockchain sectors, in particular, must remain alert to the potential risks posed by these state-sponsored operations.
In conclusion, the DPRK’s use of AI and layered malware strategies in cyber attacks represents a significant challenge to digital security. The ongoing campaigns highlight the importance of robust security practices and the need for continuous monitoring to thwart these advanced threats.