A sophisticated piece of malware known as SLOTAGENT is making waves within the cybersecurity community. Distinguished by its capacity to elude analysis and detection, SLOTAGENT employs advanced tactics rather than brute force to confound researchers. The malware’s usage of API hashing and encrypted strings creates significant challenges for reverse engineering, indicating a high level of expertise from its creators.
SLOTAGENT’s primary distribution method is through phishing emails, which often carry malicious attachments disguised as regular business documents or software updates. Once a recipient opens the attachment, the malware operates silently in the background. It promptly establishes a connection with a remote command-and-control server to receive further instructions, maintaining minimal network activity to avoid triggering security alerts. This reliance on phishing underscores the persistent effectiveness of social engineering in initial access attempts by cyber attackers.
SLOTAGENT’s Evasion Tactics
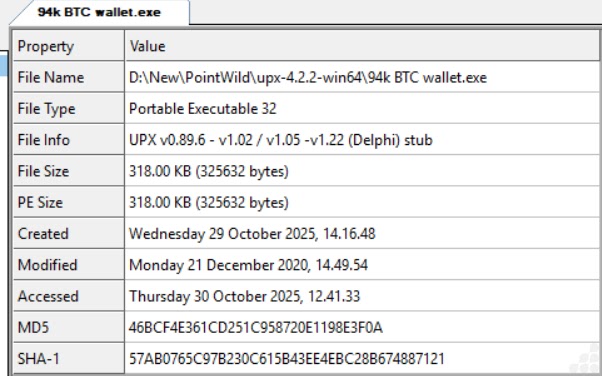
The discovery of SLOTAGENT was made by analysts at IIJ-SECT during an investigation into suspicious network activity linked to a targeted intrusion. Analysis of the malware revealed a deliberate design to hinder both static and dynamic examination. Critical information normally visible in the code was encrypted, and standard API dependencies were omitted from the import table, replaced instead by a runtime hashing process. This approach significantly complicates the task for analysts attempting to dissect the malware’s behavior.
The consequences of a SLOTAGENT infection extend beyond the technical challenges it poses to analysts. Organizations affected by this malware face immediate risks such as data breaches, unauthorized access, and the deployment of additional harmful payloads. The malware’s stealthy nature allows it to remain undetected for extended periods, potentially weeks or months, granting attackers prolonged access to sensitive data and resources, thereby exacerbating the damage inflicted.
Understanding SLOTAGENT’s Core Mechanisms
At the heart of SLOTAGENT’s ability to evade detection is its use of runtime API resolution via hashing. Unlike typical malware, which lists its required Windows API functions in a readable import table, SLOTAGENT generates a hash for each function name and searches loaded system modules to find matches. This absence of function names in the import table makes static analysis ineffective, requiring researchers to decode the hashing algorithm to proceed with their investigation.
Another key defense mechanism in SLOTAGENT is the encryption of strings. Essential data, such as server details and configuration settings, are not stored in plain text but are decrypted only when needed during execution. This strategy effectively thwarts string extraction tools used in static analysis, and even dynamic analysis can be challenging if memory capture occurs at the wrong time.
Mitigation Strategies for Security Teams
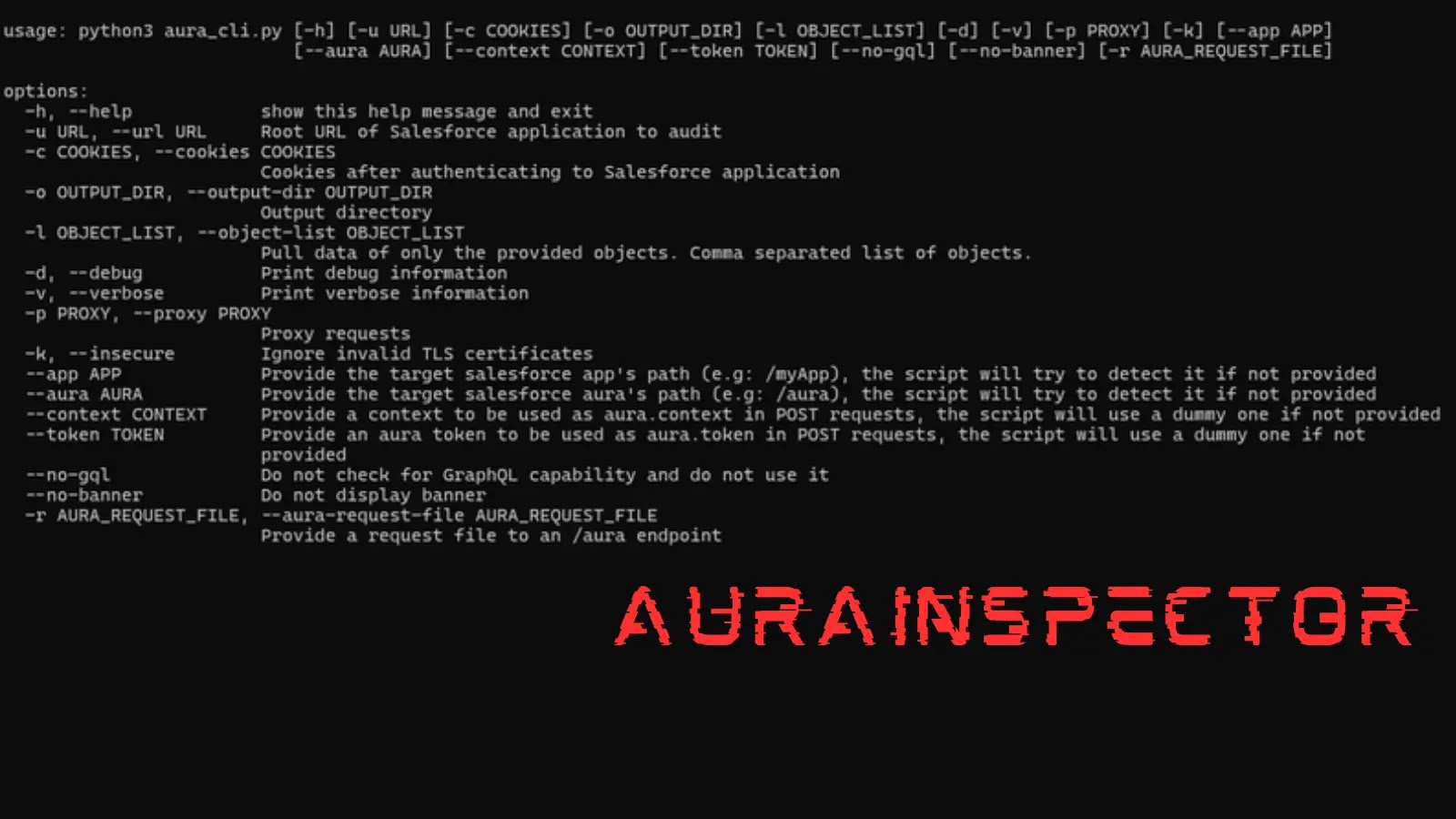
To counter SLOTAGENT, security teams should develop behavioral detection rules that focus on identifying runtime API resolution activities, rather than relying solely on signature-based methods. Monitoring for unusual memory allocations and unexpected process injections can help detect SLOTAGENT infections early. Additionally, network defenders are advised to scrutinize outbound traffic for patterns indicative of command-and-control communications, especially from processes that typically do not initiate external connections.
Keeping endpoint security tools updated and ensuring threat intelligence feeds are current are essential measures. Training staff to recognize phishing emails is also crucial, as it directly addresses the malware’s primary delivery method. By implementing these strategies, organizations can enhance their defenses against SLOTAGENT and similar threats.