Recent investigations have revealed an advanced attack campaign leveraging the Remcos RAT, a notorious tool used by cybercriminals to control infected systems and extract sensitive data. Unlike typical malware attacks, this campaign employs a sophisticated, multi-layered strategy, beginning with a phishing email and culminating in an undetectable in-memory compromise.
Advanced Threat Delivery Tactics
Remcos RAT, which stands for Remote Control and Surveillance, has been a persistent threat for several years. Traditionally used for keystroke logging and data theft, the current operation distinguishes itself through its intricate delivery methods. The attackers utilize a series of obfuscation techniques, trusted Windows binaries, and a live command-and-control (C2) server to effectively deliver their payload.
Researchers from Point Wild’s LAT61 Threat Intelligence Team identified this campaign by analyzing a malicious email (.eml) file. The attack initiates with a ZIP file named “MV MERKET COOPER SPECIFICATION.zip,” masquerading as a typical business document to lure victims into execution.
In-Depth Analysis of the Infection Chain
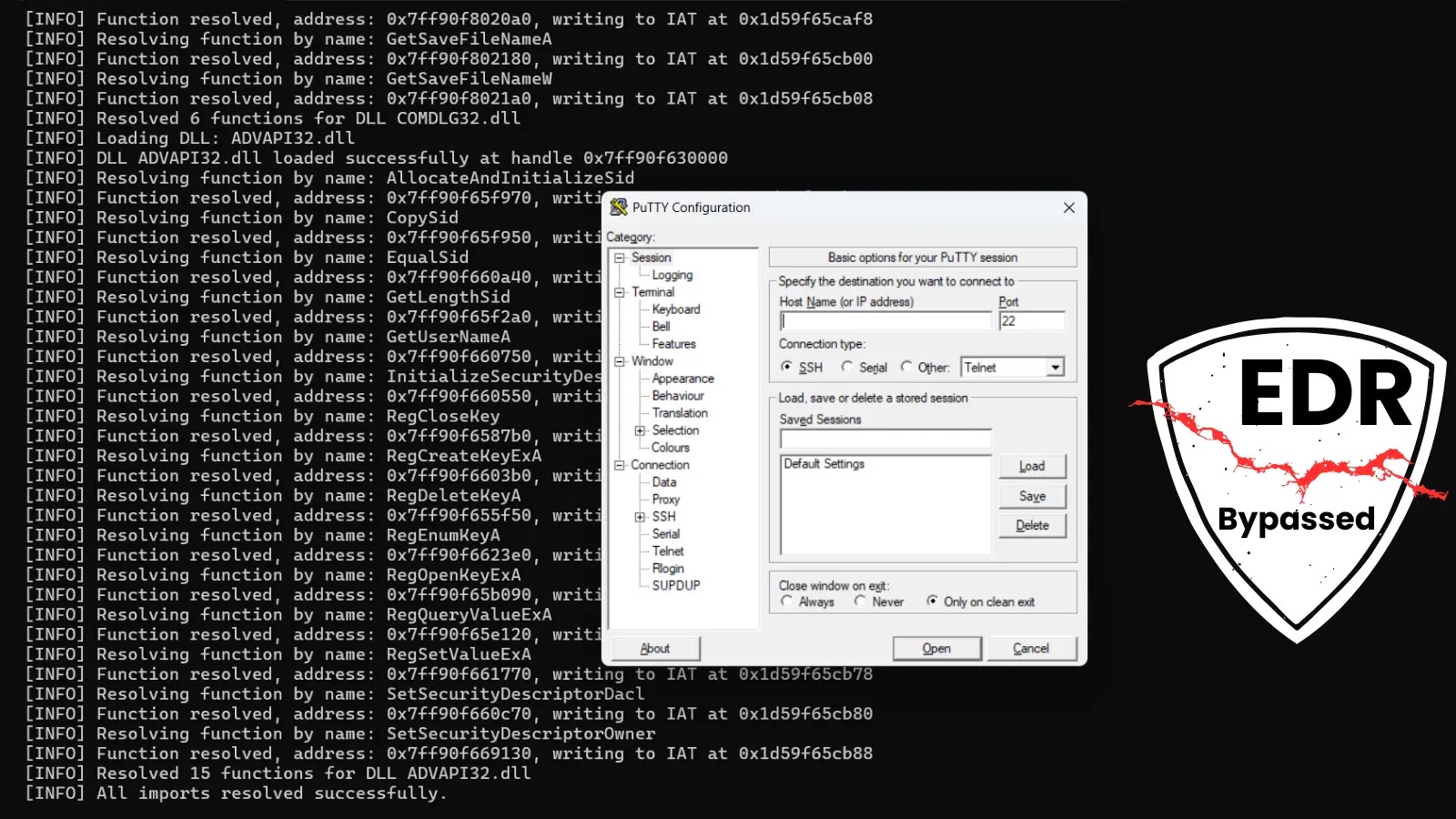
Upon opening the ZIP attachment, an obfuscated JavaScript file is deployed, silently setting the attack in motion without triggering standard security alerts. The script, executed via Windows Script Host, establishes communication with a remote server to download a PowerShell script, furthering the attack.
Key to the attack’s success is its use of legitimate system tools and memory-based execution, allowing the malware to evade traditional detection methods. The JavaScript creates ActiveX objects for HTTP communication and file operations while contacting almacensantangel[.]com to retrieve an encrypted payload.
Implications and Defensive Measures
Once deployed, Remcos RAT establishes a persistent connection to a remote C2 server, enabling continuous data exfiltration. Security researchers confirmed data collection through a log file at C:ProgramDataremcoslogs.dat, which stores captured keystrokes and system information.
Organizations are advised to monitor PowerShell execution events, especially those involving Base64-encoded commands, and scrutinize outbound connections from system utilities like aspnet_compiler.exe. Recognizing and blocking known malicious URLs and C2 infrastructure are essential steps in mitigating this threat.
In conclusion, the Remcos RAT campaign exemplifies the evolving nature of cyber threats, emphasizing the need for enhanced security measures and vigilance. As cybercriminals continue to refine their tactics, organizations must remain proactive in their defense strategies to protect sensitive information.