A significant cybersecurity breach has come to light, with threat actors exploiting a vulnerability known as React2Shell to penetrate Next.js applications. This breach has enabled attackers to extract sensitive data such as database credentials, SSH keys, and API secrets from numerous systems.
Details of the Exploitation
The operation, tracked by Cisco Talos as UAT-10608, has compromised at least 766 hosts across various cloud environments. The attackers utilized automated scripts to exfiltrate credentials and relay them to a command-and-control (C2) server, which uses a graphical interface termed ‘NEXUS Listener’ to manage the stolen data.
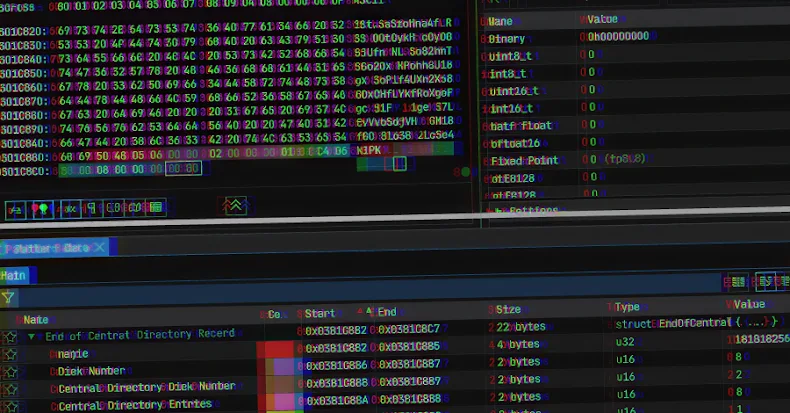
The attack primarily targets a critical vulnerability, CVE-2025-55182, in React Server Components and Next.js App Router, which has a CVSS score of 10.0 indicating severe risk. This flaw allows remote code execution, facilitating unauthorized access and subsequent deployment of a collection framework called NEXUS Listener.
Mechanisms of Data Extraction
The threat actors employed a multi-stage script to gather a wide range of data from infected systems. This includes environmental variables, SSH keys, shell history, Kubernetes tokens, and configuration details of Docker containers. Additionally, they harvested API keys and temporary credentials by querying cloud services like AWS and Azure.
The attackers leveraged tools like Shodan and Censys to identify vulnerable Next.js deployments, scanning for exposed systems that could be easily compromised. The NEXUS Listener interface provides a detailed overview of the stolen credentials and compromised hosts, revealing the scale of the operation.
Implications and Recommendations
The breach exposes the breadth of sensitive data that can be accessed by exploiting such vulnerabilities. Organizations are urged to review their security measures, enforce strict privilege policies, and rotate credentials regularly. Implementing security measures such as secret scanning and utilizing IMDSv2 for AWS instances are recommended to mitigate potential threats.
The stolen data not only holds immediate operational value but also offers insights into the targeted organizations’ infrastructure, revealing configurations and third-party integrations. This intelligence can be exploited for further attacks, underscoring the need for robust cybersecurity practices.
The ongoing development of tools like NEXUS Listener highlights the evolving capabilities of cyber attackers, necessitating continuous vigilance and proactive security strategies. Organizations should remain alert to emerging threats and ensure their systems are fortified against potential breaches.