Amazon Web Services (AWS) has issued a critical security update for its Research and Engineering Studio (RES), addressing three major vulnerabilities. These security flaws could potentially allow authenticated users to execute commands with root access and escalate privileges within compromised cloud environments.
Understanding the AWS RES Platform
AWS Research and Engineering Studio serves as an open-source web portal designed to aid administrators in building, managing, and expanding secure cloud-based research and engineering solutions. Given the sensitive nature of the data often handled by these environments, AWS urges immediate application of the latest security patches.
Detailed Analysis of Vulnerabilities
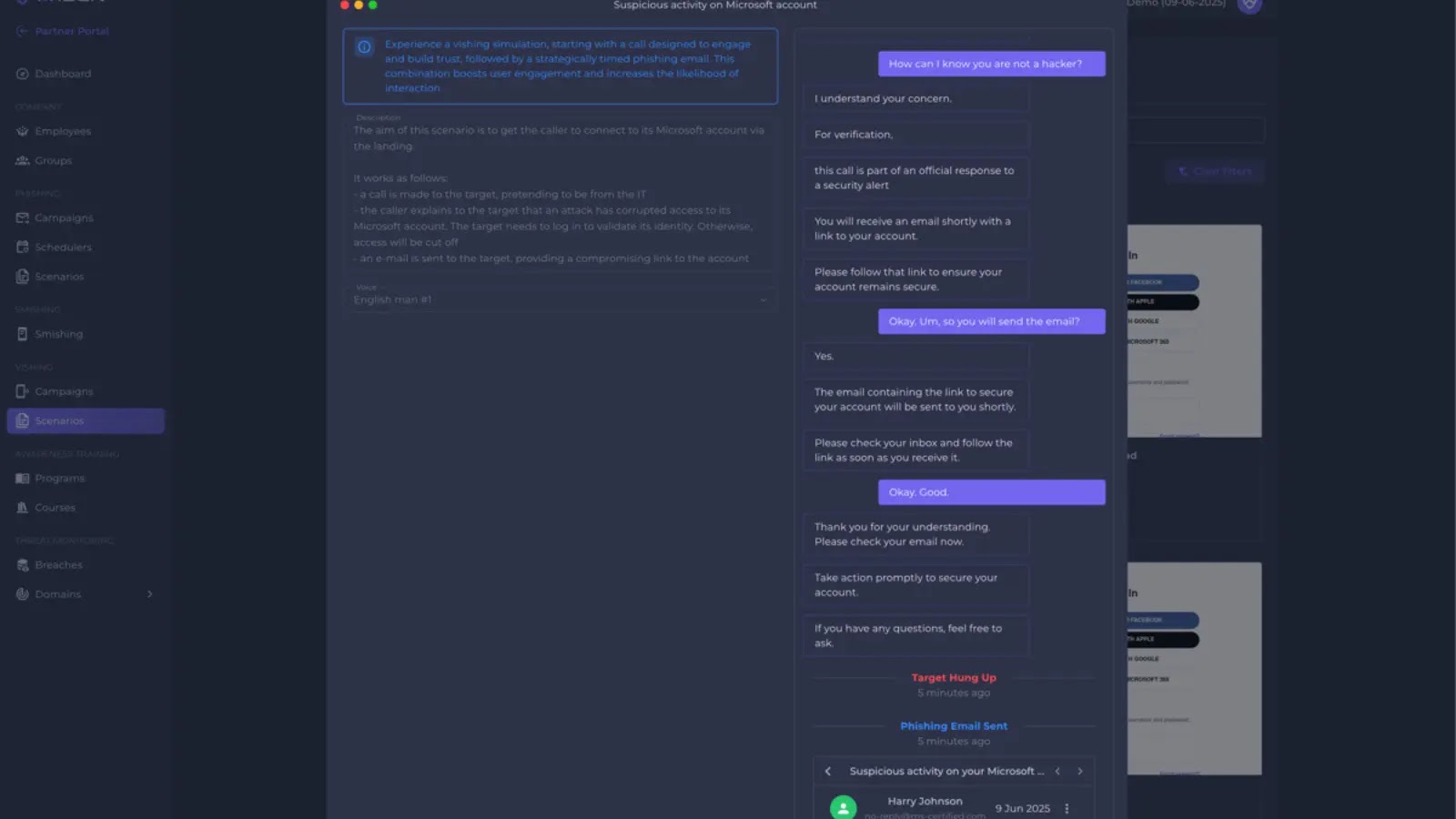
The security bulletin, identified as 2026-014-AWS, outlines three vulnerabilities targeting RES versions 2025.12.01 and earlier. Despite requiring authenticated access, these vulnerabilities present significant risks for network compromise.
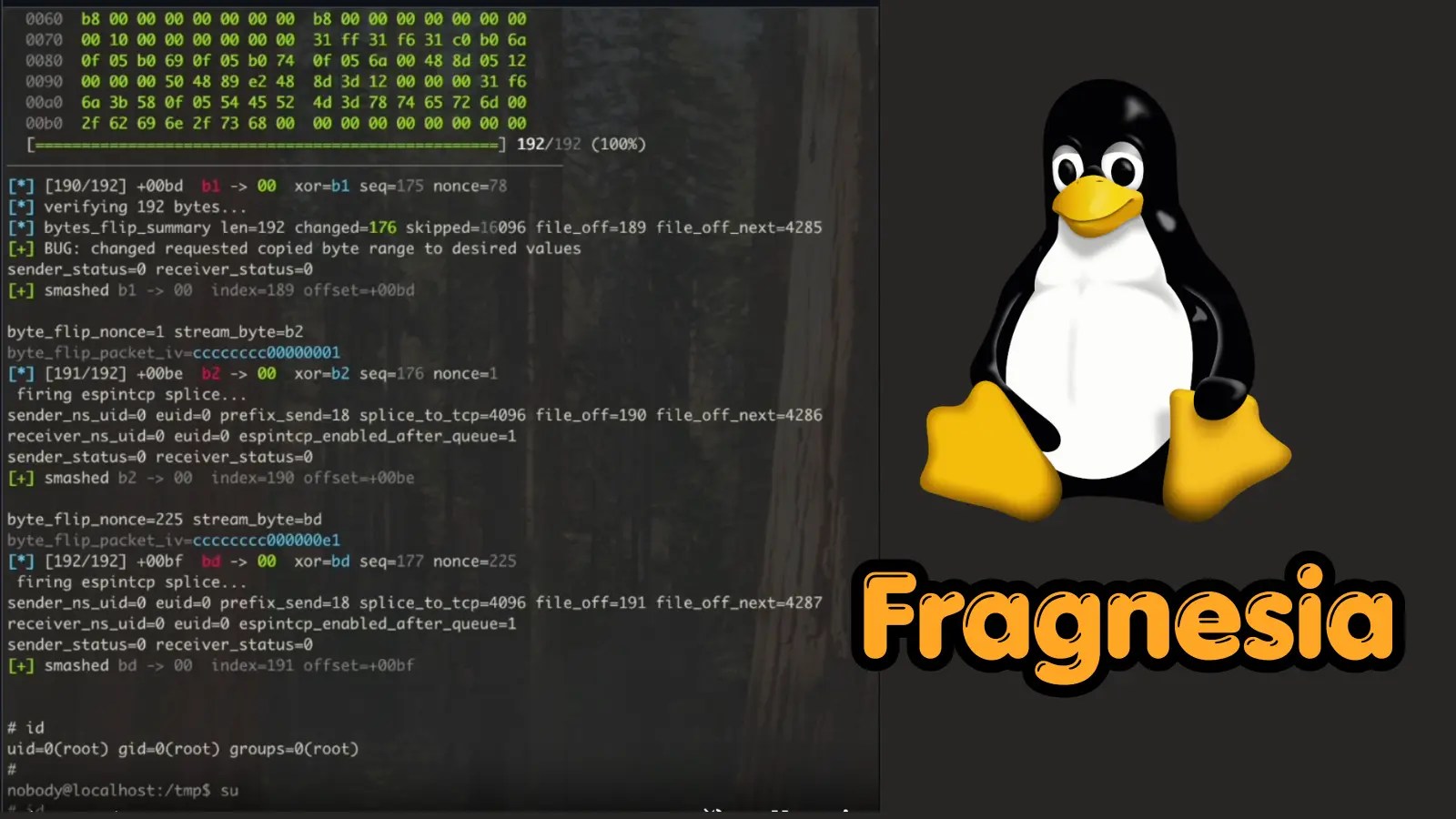
CVE-2026-5707: This flaw arises from improper input sanitation in virtual desktop session names, allowing attackers to execute arbitrary commands with root privileges on the virtual desktop host. This affects versions from 2025.03 to 2025.12.01.
CVE-2026-5708: Involving improper control of user attributes during session creation, this vulnerability enables a remote user to escalate privileges, gaining unauthorized access to AWS resources. It impacts all versions before 2026.03.
Impact and Remediation Measures
If left unresolved, these vulnerabilities could permit attackers to compromise virtual desktop hosts, control the cluster manager, and access other sensitive AWS resources. Such breaches could result in data exposure or operational disruptions.
AWS has resolved these issues in RES version 2026.03. Organizations are advised to upgrade to this version promptly. For those using customized versions, integrating these security patches is essential to prevent exposure.
Mitigation Strategies for Immediate Action
For teams unable to upgrade immediately, AWS provides manual workarounds. Administrators can implement specific patches by following the mitigation instructions available on the AWS RES GitHub repository. These fixes address key vulnerabilities, ensuring platform security until a comprehensive upgrade is possible.
Stay updated with our daily cybersecurity news by following us on Google News, LinkedIn, and X. For media inquiries or to feature your stories, feel free to get in touch.