Spoofed Microsoft SharePoint notifications have been a well-recognized lure for company customers, however a wave of campaigns traced between March and July 2025 exhibits a pointy uptick in each quantity and class.
The operators register look-alike domains comparable to “sharepoint-online-docs-secure[.]co” and “files-share-portal-m365[.]io,” then embed them in convincing e-mails that go SPF and DKIM checks, slipping previous perimeter filters.
As soon as a recipient clicks, the chain quietly redirects by way of a number of disposable monitoring hosts earlier than presenting an virtually pixel-perfect SharePoint login clone—full with Microsoft Viva branding—to reap credentials and session cookies.
Not like earlier credential-harvesting kits, these pages instantly set off a secondary immediate that mimics Microsoft’s push-based two-factor authentication (2FA). Victims are informed {that a} “new sign-in try from Edge on Home windows” wants approval.
In the event that they comply, attackers intercept each password and one-time token in actual time, permitting seamless entry to SharePoint, Groups, and the broader M365 tenant.
Any.Run analysts recognized the infrastructure after noticing similar JavaScript beacons calling again to cdn.alboompro[.]com/property/js/auth2fa.js, a file hosted on Alboompro’s authentic content-distribution community however abused by way of an unsecured add endpoint.
These identical analysts famous that the domains share a slender registration window—typically
DNS telemetry revealed that the majority domains resolve by way of bulletproof VPS suppliers in Jap Europe, with a lifetime shorter than 5 days, hampering block-lists.
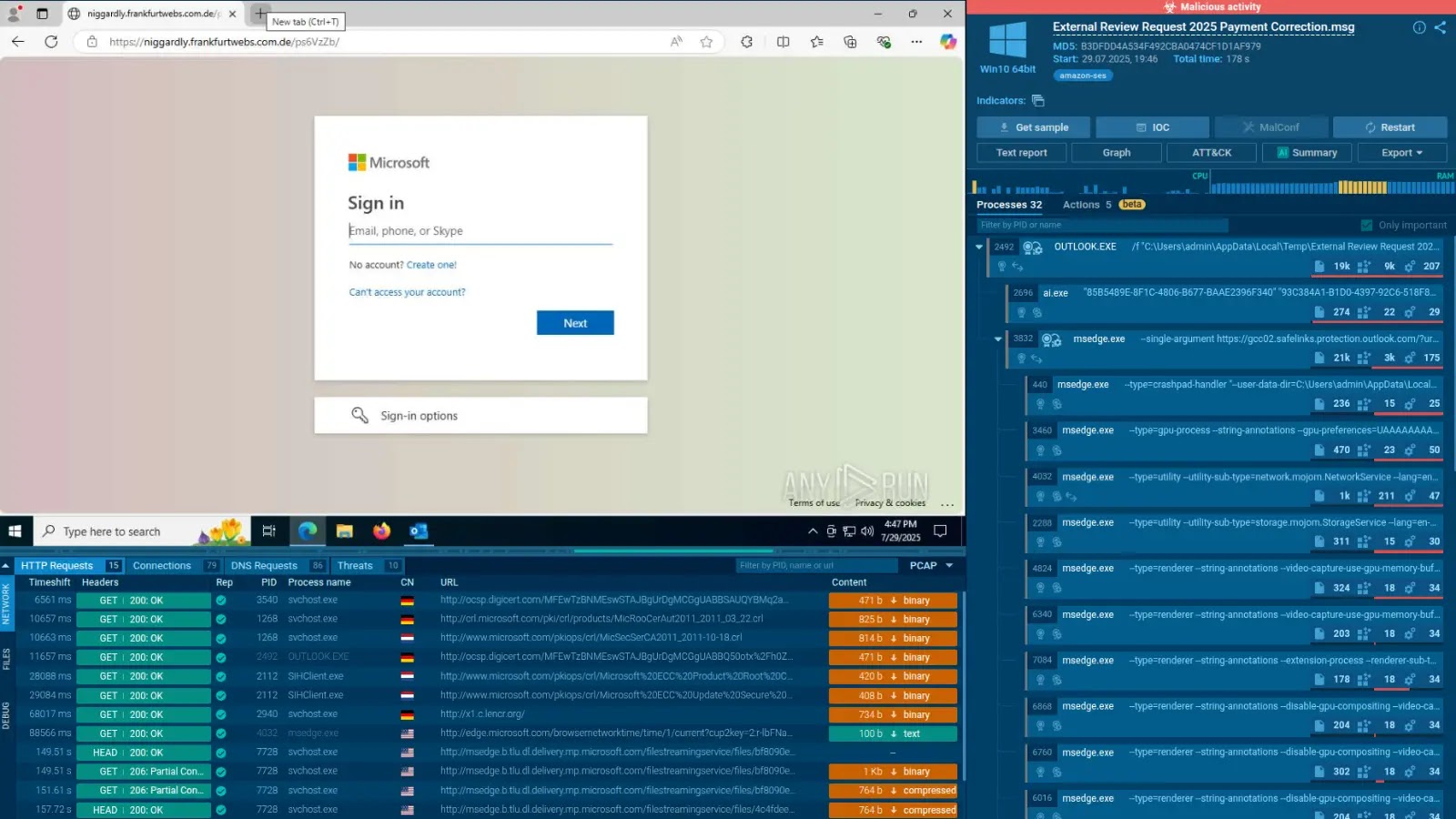
Faux PDF doc (Supply – Any.Run)
This PDF doc illustrates the beaconing sequence captured throughout sandbox detonation.
An infection Mechanism: Actual-Time Proxying of MFA Tokens
On the coronary heart of the marketing campaign is a clear reverse-proxy written in Node.js that relays all sufferer site visitors to Microsoft’s authentic login endpoint whereas siphoning tokens.
The proxy injects two scripts: one which captures the loginfmt and passwd POST parameters and one other that hooks the verificationPayload in the course of the 2FA step.
The code fragment under, recovered from a dwell server, highlights the essential intercept:-
proxy.on(‘response’, (ctx, callback) => {if (ctx.clientToProxyRequest.url.consists of(‘/login’)) {const physique = ctx.proxyToServerRequestBody.toString();const creds = physique.match(/loginfmt=(.?)&passwd=(.?)&/);save(creds[1], creds[2]); // exfiltrate credentials}if (ctx.clientToProxyRequest.url.consists of(‘/SecondFactorAuth’)) {const token = JSON.parse(ctx.proxyToServerResponseData).proof;saveMfaToken(token); // steal 2FA token}return callback();});
As a result of the proxy maintains a dwell TLS session with Microsoft on the backend, each safety header—together with HSTS and Content material-Safety-Coverage—seems intact to the browser, defeating most client-side anomaly scanners.
Moreover, the script deletes its personal deployment path after every session, leaving solely ephemeral logs in reminiscence, which vanish upon VPS re-imaging.
Early detection hinges on pattern-matching the SharePoint decoy URLs. A strong starter YARA rule launched by Any.Run researchers flags the attribute mix of /_layouts/15/begin.aspx and the rogue 2FA script hash, offering SOC groups an instantaneous looking deal with.
Till identification suppliers undertake origin-bound tokens and mitigations comparable to Steady Entry Analysis, organizations should mix area age filtering with user-reported MFA fatigue indicators to cut back publicity to this fast-moving risk.
Expertise sooner, extra correct phishing detection and enhanced safety for your small business with real-time sandbox analysis-> Attempt ANY.RUN now