Two rogue Chrome extensions have compromised over 900,000 customers by secretly exfiltrating ChatGPT and DeepSeek conversations, together with full searching histories, to attacker servers.
Found by OX Safety researchers, the malware impersonates the respectable AITOPIA AI sidebar software, with one faux even incomes Google’s “Featured” badge.
The OX Analysis group recognized the menace throughout routine evaluation, revealing extensions that clone AITOPIA’s interface for chatting with LLMs like GPT and Claude.
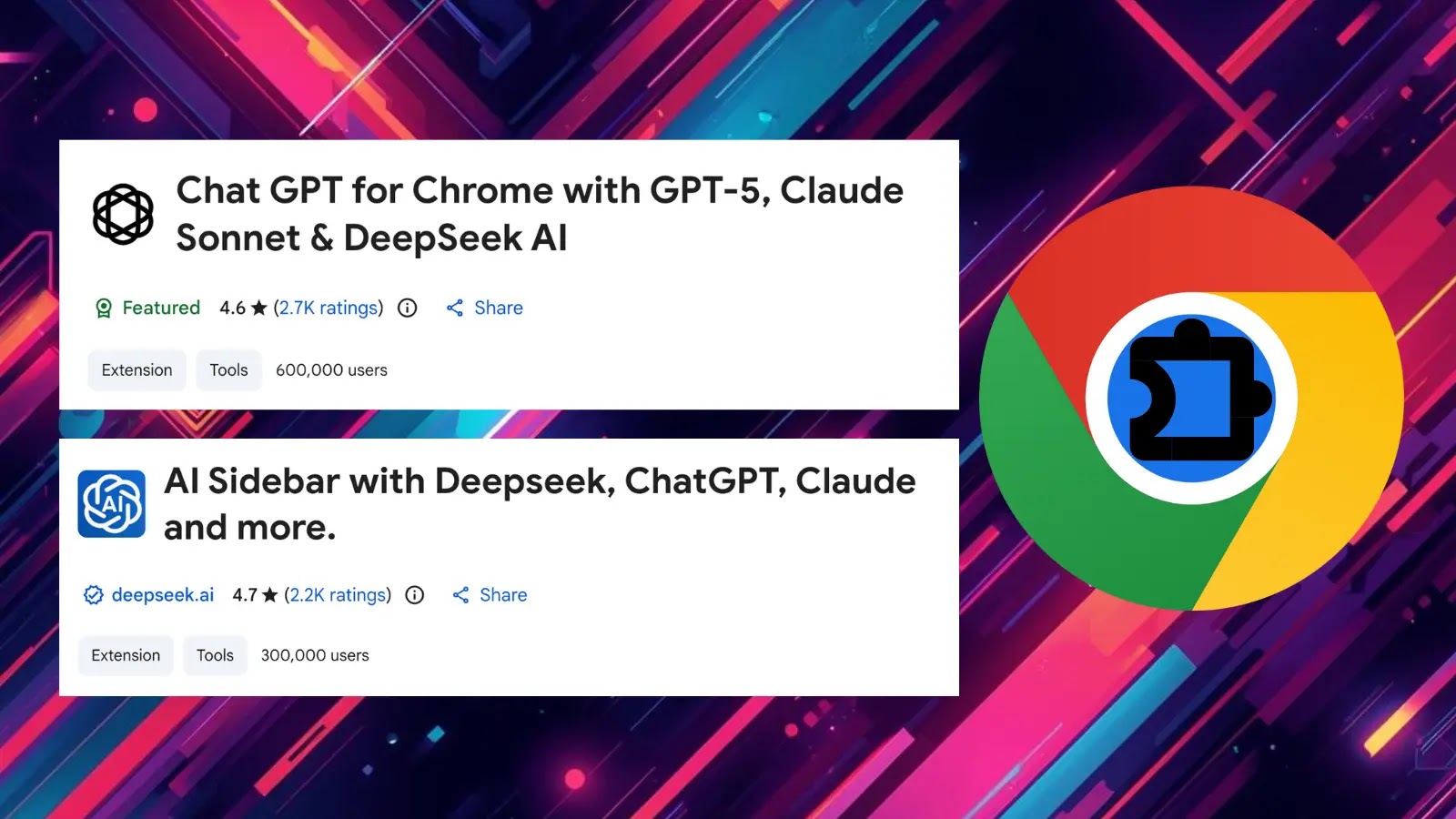
Named “Chat GPT for Chrome with GPT-5, Claude Sonnet & DeepSeek AI” (600K+ customers, ID: fnmihdojmnkclgjpcoonokmkhjpjechg, model 1.9.6) and “AI Sidebar with Deepseek, ChatGPT, Claude and extra” (300K+ customers, ID: inhcgfpbfdjbjogdfjbclgolkmhnooop), they request “nameless analytics” consent to masks knowledge theft.
Risk actors host privateness insurance policies on Lovable.dev to obscure origins, and uninstalled extensions redirect to the opposite.
How the Malware Operates
Put in extensions monitor tabs by way of chrome.tabs.onUpdated API, producing a novel “gptChatId” per sufferer. On detecting chatgpt.com or deepseek.com URLs, they scrape DOM parts for prompts, responses, and session IDs, storing knowledge domestically earlier than Base64-encoding and sending batches to C2 servers like deepaichats.com or chatsaigpt.com each half-hour.
This captures proprietary code, enterprise methods, PII, search queries, and inside URLs missed by AITOPIA’s disclosed server storage.
Stolen chats threat exposing mental property, company secrets and techniques, and private knowledge for espionage or sale on darkish internet boards. Searching logs reveals habits, tokens, and org constructions, enabling phishing or id theft throughout affected enterprises.
As of January 7, 2026, each extensions stay downloadable, with the primary stripped of its “Featured” standing post-disclosure however up to date as not too long ago as October 2025.
Customers ought to go to chrome://extensions, take away by ID, or use retailer pages: ChatGPT extension, AI Sidebar. Keep away from unverified extensions no matter badges; stick with respected sources.
IoCs
TypeValueNotesExtension nameChat GPT for Chrome with GPT-5, Claude Sonnet & DeepSeek AIMalicious AI sidebar-style extensionExtension IDfnmihdojmnkclgjpcoonokmkhjpjechgChrome Net Retailer IDVersion1.9.6Reported malicious buildSHA-256 hash98d1f151872c27d0abae3887f7d6cb6e4ce29e99ad827cb077e1232bc4a69c00Package hashExtension nameAI Sidebar with Deepseek, ChatGPT, Claude and moreSecond malicious extensionExtension IDinhcgfpbfdjbjogdfjbclgolkmhnooopChrome Net Retailer IDVersion1.6.1Reported malicious buildSHA-256 hash20ba72e91d7685926c8c1c5b4646616fa9d769e32c1bc4e9f15dddaf3429cea7Package hash
Community and C2 IoCs
CategoryDomain / EndpointNotesC2 endpointdeepaichats[.]comReceives stolen chat knowledge and URLsC2 endpointchatsaigpt[.]comAdditional C2 for exfiltrated dataLovable-hosted serverchataigpt[.]proUsed for privateness coverage / infra hostingLovable-hosted serverchatgptsidebar[.]proUsed for uninstall redirect and infra
Comply with us on Google Information, LinkedIn, and X for each day cybersecurity updates. Contact us to characteristic your tales.