In the field of managed security services, ensuring comprehensive protection for clients hinges on continuous visibility into potential threats. Real-time threat visibility has become crucial for Managed Security Service Providers (MSSPs) to enhance their defensive measures. By integrating live threat intelligence, MSSPs can address vulnerabilities and minimize risks more effectively.
The Visibility Challenge in Managed Security
MSSPs operate in a dynamic environment where vast amounts of data must be processed quickly. With thousands of endpoints and diverse customer environments, security operations centers (SOCs) face challenges such as alert fatigue and aggressive service level agreements (SLAs). Statistics reveal that an average SOC encounters around 11,000 alerts daily, yet only roughly 19% are worth investigating. The remaining alerts consume valuable analyst time, diluting attention from more critical threats.
The most damaging threats often go unnoticed as they do not trigger immediate alerts. This lack of detection is largely due to outdated indicators of compromise (IOCs) and lagging intelligence. Addressing this gap requires continuously updated data that is behaviorally grounded and integrated across core workflows. Live Threat Intelligence Feeds are essential in solving these visibility issues.
Importance of Data Quality and Timeliness
The effectiveness of threat detection heavily depends on the quality and speed of data. IOCs detected after an attack has commenced may assist in retrospective analysis but often arrive too late to prevent compromise. MSSPs need intelligence generated during active campaigns to preemptively halt threats.
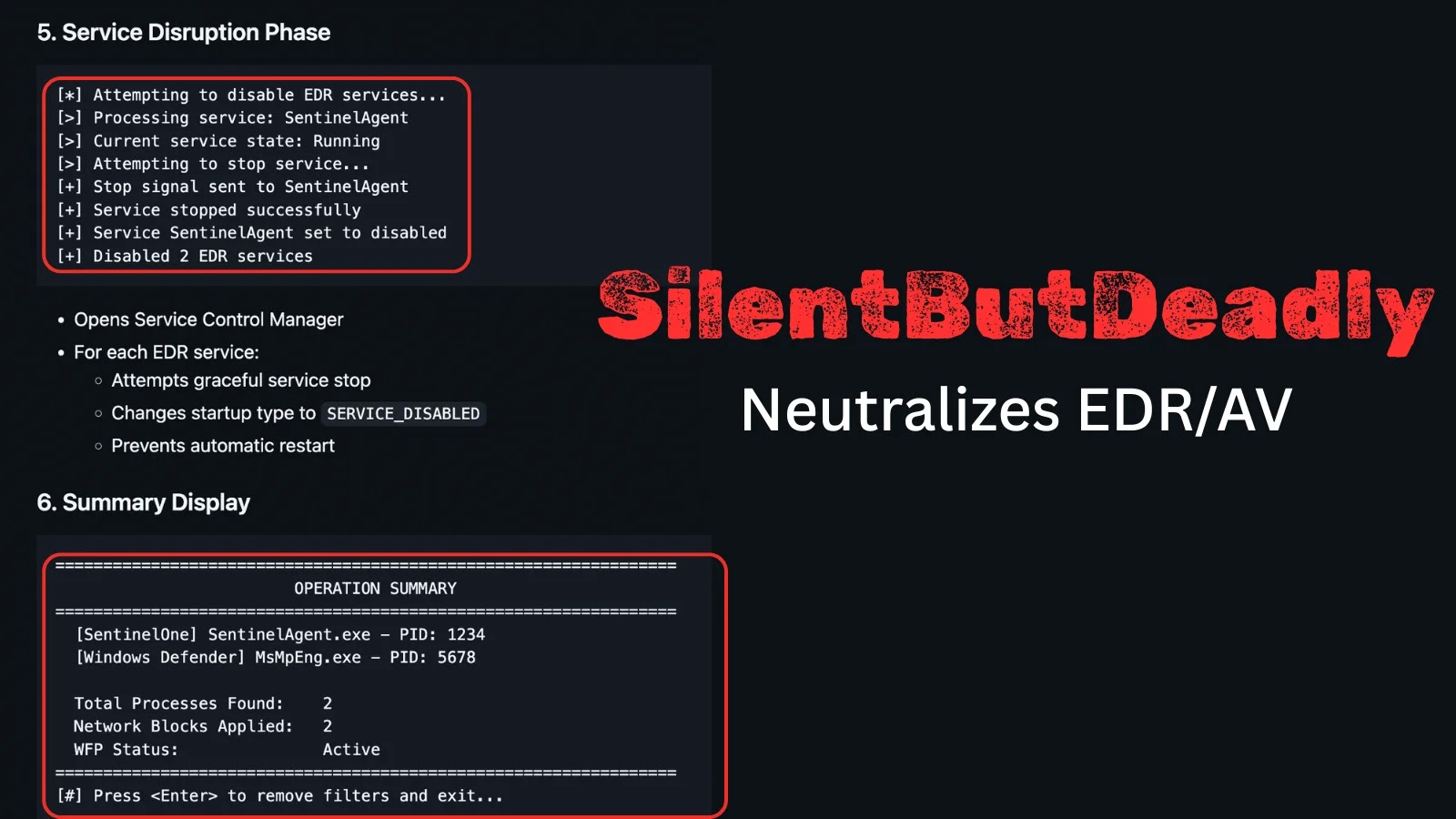
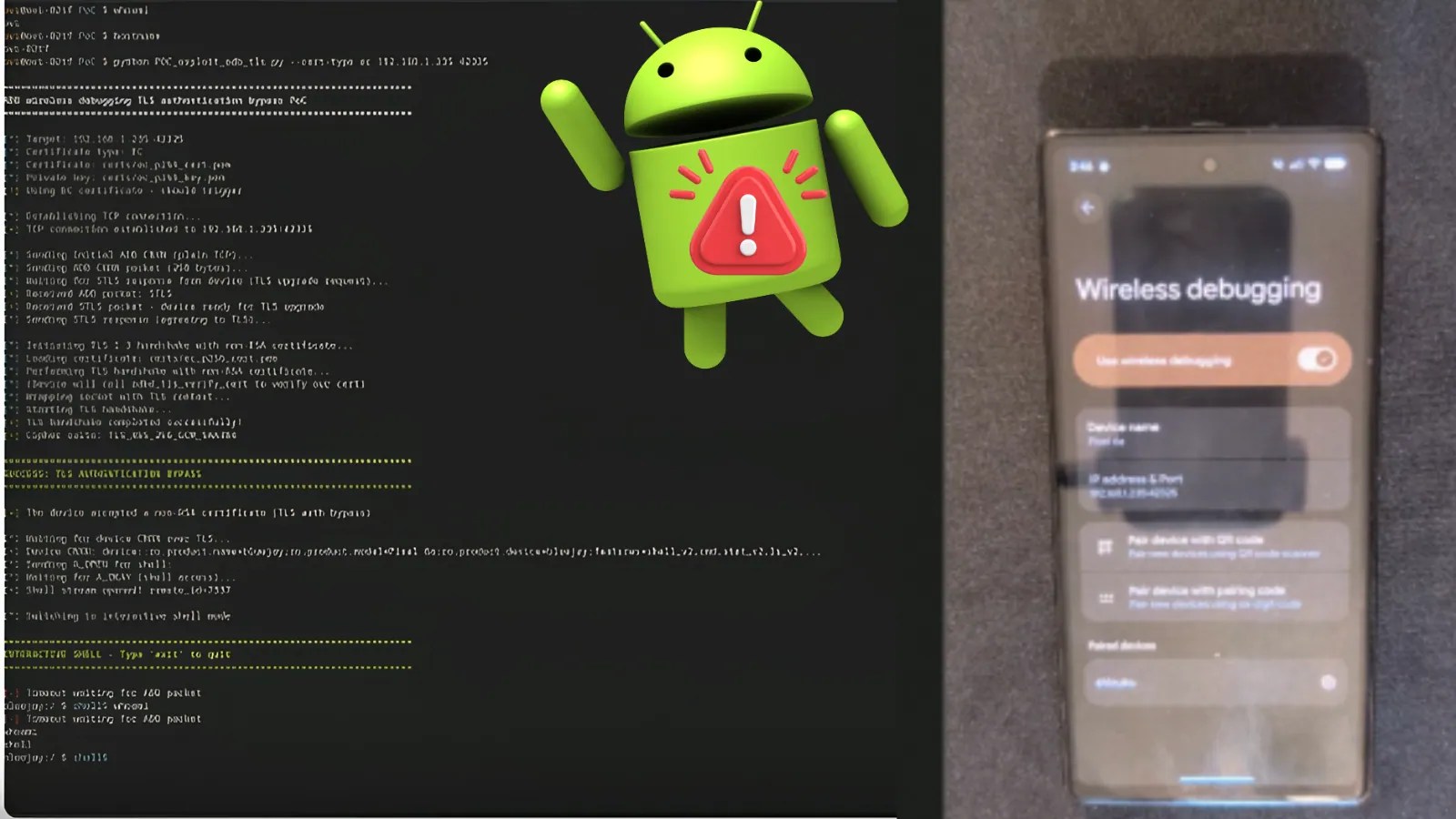
Key attributes of an effective threat intelligence pipeline include real-time data collection, continuous malware detonation, automated IOC extraction, and rapid feed distribution. This approach allows MSSPs to capture attacker infrastructure as it unfolds, enabling proactive measures such as stopping credential theft or detecting ransomware staging at early stages.
Integrating Live Threat Intelligence Feeds
Live Threat Intelligence Feeds fill critical blind spots in SOC and MSSP processes. Traditional signature-based detection methods often lag behind evolving threats, creating exposure windows. By integrating fresh IOC feeds, MSSPs can immediately correlate data in SIEM, IDS/IPS, and SOAR systems, mitigating blind spots in perimeter and endpoint monitoring.
For incident response, pre-validated IOCs with behavioral context expedite containment decisions. This integration allows analysts to verify indicators, understand attacker intent, and assess the scope of incidents promptly. The result is a significant reduction in mean time to detect (MTTD) and mean time to respond (MTTR), improving overall security posture.
Future Outlook: Continuous Improvement and Client Assurance
For MSSPs, demonstrating value through continuous improvement and client assurance is paramount. Live feeds not only increase detection rates but also reduce analysis time, providing evidence-based reports of blocked threats. This proactive approach strengthens client relationships and enhances competitive positioning.
Integrating Threat Intelligence Feeds does not disrupt existing workflows. Formats like STIX/TAXII and MISP ensure seamless integration with current platforms, facilitating automation and customization without additional complexity. By closing intelligence gaps with fresh, verified data, MSSPs can transition from reactive incident response to proactive threat prevention, securing their position as leaders in cybersecurity.