The FBI’s Atlanta Field Office has partnered with Indonesian law enforcement to successfully dismantle a significant global phishing operation. This unprecedented collaboration focused on the notorious W3LL phishing kit, a toolset notorious for its capability to bypass multi-factor authentication and facilitate financial fraud attempts totaling over $20 million.
Breaking New Ground in Cybercrime Prevention
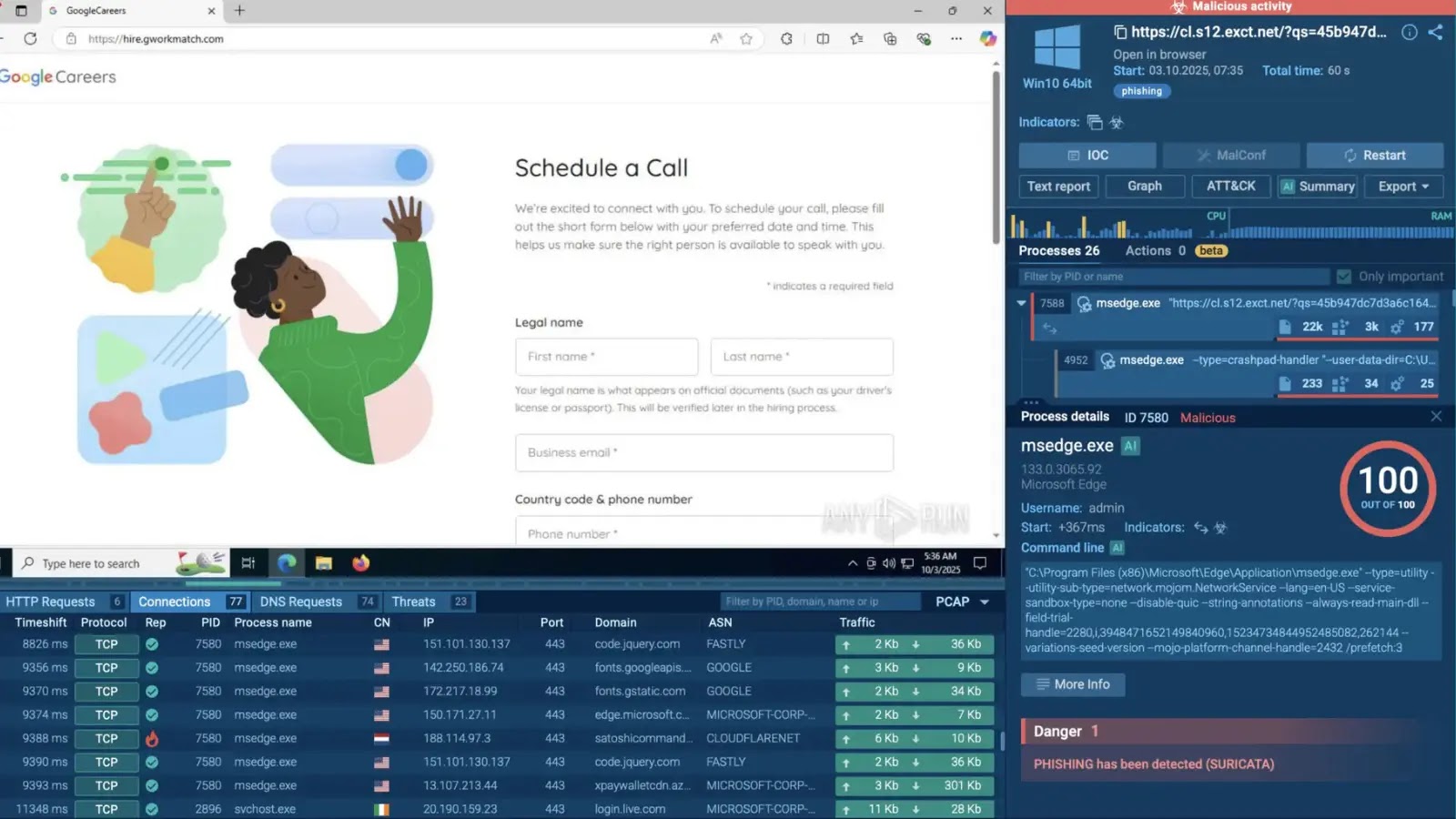
This case marks the first concerted effort between the United States and Indonesia targeting a phishing kit developer. The W3LL phishing kit functioned as a cybercrime-as-a-service platform, making sophisticated hacking techniques accessible to even novice cybercriminals. For approximately $500, buyers could deploy convincing fake websites mimicking trusted corporate login portals, with the kit’s most dangerous feature being its ability to circumvent modern security measures.
Once victims entered their credentials on these fraudulent sites, the toolkit went beyond harvesting basic information by capturing session cookies and authentication tokens. This allowed attackers to bypass multi-factor authentication seamlessly, maintaining unauthorized access without triggering security alerts.
The Impact and Reach of W3LLSTORE
The W3LL operation was bolstered by an online marketplace known as W3LLSTORE, a dark web hub offering stolen credentials, unauthorized corporate system access, and remote desktop connections. The marketplace’s influence was significant across the cyber threat landscape globally. Between 2019 and 2023, over 25,000 compromised accounts were sold through this platform.
From 2023 to 2024, the rebranded phishing kit targeted more than 17,000 victims worldwide, enabling over $20 million in fraudulent attempts. The developer of the kit clandestinely collected and resold access to these compromised accounts, effectively profiting twice from the stolen data.
Arrests and Seizures Mark a Major Victory
Although W3LLSTORE shut down in 2023, its operations persisted on encrypted messaging forums. Investigators diligently tracked the rebranded network, ultimately tracing it back to key individuals. With crucial support from the U.S. Attorney’s Office for the Northern District of Georgia, the FBI managed to identify and seize the core infrastructure that facilitated these phishing activities.
During a coordinated operation, the Indonesian National Police apprehended the alleged developer, identified as G.L., while seizing vital domains linked to the network. Marlo Graham, Special Agent in Charge at the FBI Atlanta office, described the operation as a comprehensive cybercrime platform rather than a mere phishing tool. By dismantling this infrastructure, authorities have significantly disrupted a critical resource for cybercriminals seeking to infiltrate corporate networks.
Stay informed with our updates on Google News, LinkedIn, and X. Reach out to us to feature your cybersecurity stories.