Hackers have launched a classy phishing marketing campaign exploiting Google Duties notifications to focus on over 3,000 organizations worldwide, primarily within the manufacturing sector.
The December 2025 assaults sign a harmful shift in email-based threats, during which attackers abuse professional Google infrastructure slightly than spoofing domains or forging electronic mail headers.
The phishing emails originated from a professional Google handle [email protected] and efficiently handed all main electronic mail authentication protocols, together with SPF, DKIM, DMARC, and CompAuth.
This allowed malicious messages to bypass conventional electronic mail safety gateways that depend on sender fame and area belief, RavenMail instructed Cybersecurity Information.
Google Duties Notification Primarily based Assault
The emails impersonated Google Duties notifications, presenting what seemed to be an “All Workers Activity” requesting pressing worker verification.
Recipients had been prompted to click on buttons labeled “View job” or “Mark full,” which redirected them to a malicious web page hosted on Google Cloud Storage.
Phishing Marketing campaign Exploits Trusted Google Service
Attackers exploited Google’s Software Integration service to ship emails from professional Google infrastructure, inheriting Google’s excessive sender fame and common allowlisting.
The phishing web page replicated Google Duties branding with excessive accuracy, together with acquainted UI components, professional footer textual content, and authentic-looking call-to-action buttons.
The assault redirected victims to URLs hosted on Google Cloud Storage (storage.cloud.google.com), rendering conventional URL-reputation-based detection ineffective.
The messages used psychological triggers, together with authority framing, urgency indicators, and minimal clarification, to encourage speedy motion with out scrutiny. This assault represents a basic problem to electronic mail safety.
For the reason that sender was Google, authentication checks handed, domains had been trusted, and no suspicious attachments had been current, typical safety instruments discovered nothing to dam.
Menace researchers have documented related campaigns that abuse Google Classroom, Google Types, and AppSheet to reap credentials.
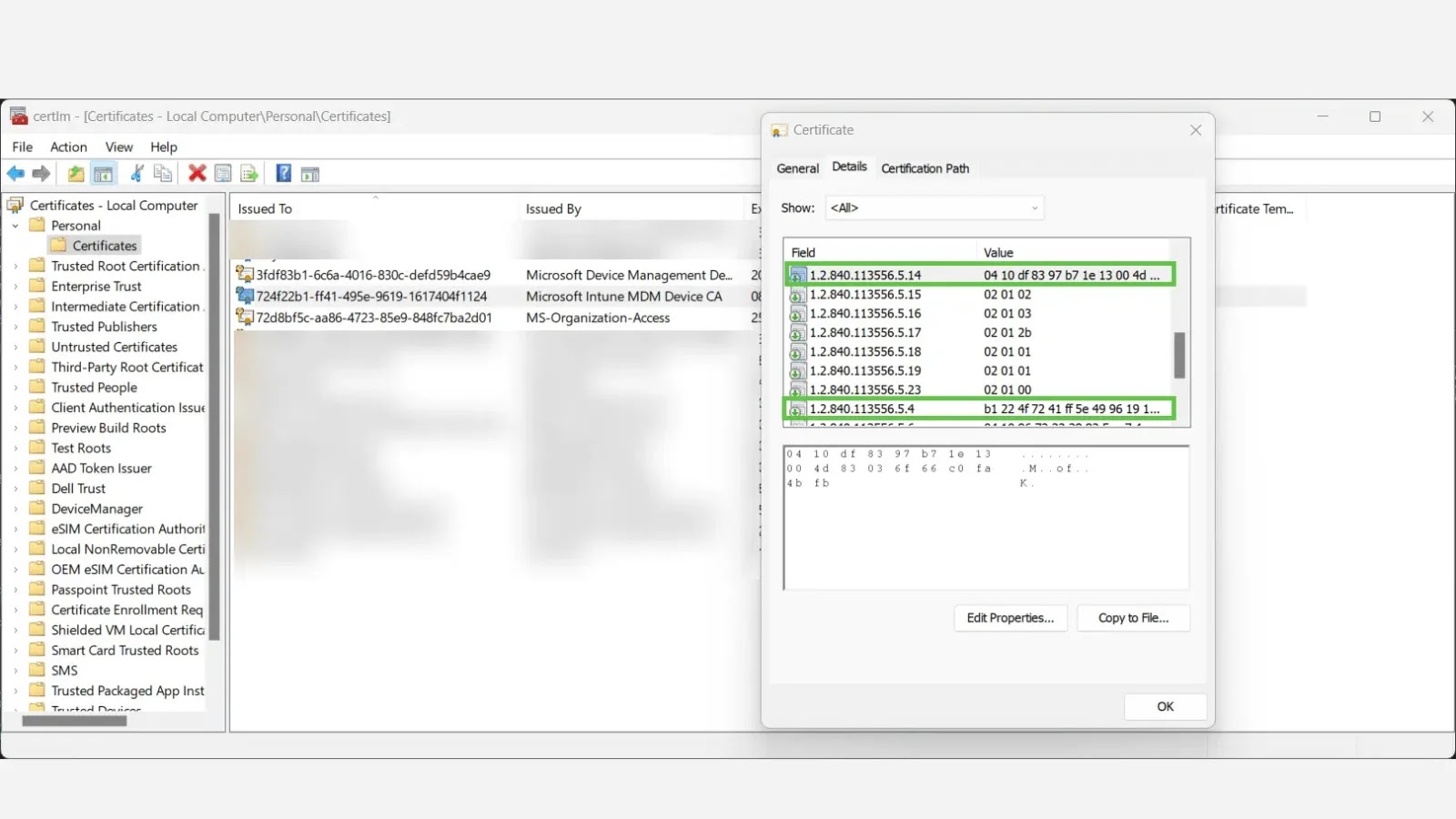
Mail ship workflows from Software Integration Service
RavenMail detected the marketing campaign by analyzing contextual mismatches slightly than counting on area fame.
The safety platform recognized that Google Duties was getting used for HR verification as anomalous and that Cloud Storage URLs had been inconsistent with professional Google Duties workflows. Safety consultants warn that this isn’t remoted to Google.
Attackers are more and more abusing trusted platforms, together with Salesforce and Amazon SES, to ship phishing assaults inside professional techniques.
The shift from infrastructure-level spoofing to workflow abuse requires organizations to rethink electronic mail safety past conventional authentication alerts.
Comply with us on Google Information, LinkedIn, and X for each day cybersecurity updates. Contact us to function your tales.