An extensive malware campaign has been unearthed, involving 109 counterfeit GitHub repositories employed to disseminate two hazardous malware tools known as SmartLoader and StealC. These repositories were designed to deceive users by mimicking legitimate open-source projects, making it difficult for the average individual to distinguish between authentic and fraudulent content.
Deceptive Tactics in Repository Cloning
The perpetrators of this scheme replicated genuine GitHub projects, re-uploading them under new accounts, and substituting the original documentation with download links leading to malicious ZIP files. These files were strategically concealed within the repository’s folder structures, resembling standard release packages. The genuine source code was largely preserved, lending an air of authenticity to these fake repositories at first glance.
Hexastrike analysts identified these 109 malicious repositories spread across 103 distinct GitHub accounts. The operation appeared to have been active for at least seven weeks before their assessment, with new repositories continuing to emerge as of April 12, 2026. The pattern of repository updates, including rotating download links, suggested centralized control and partial automation by a single entity or a closely knit group.
Impact and Methods of Operation
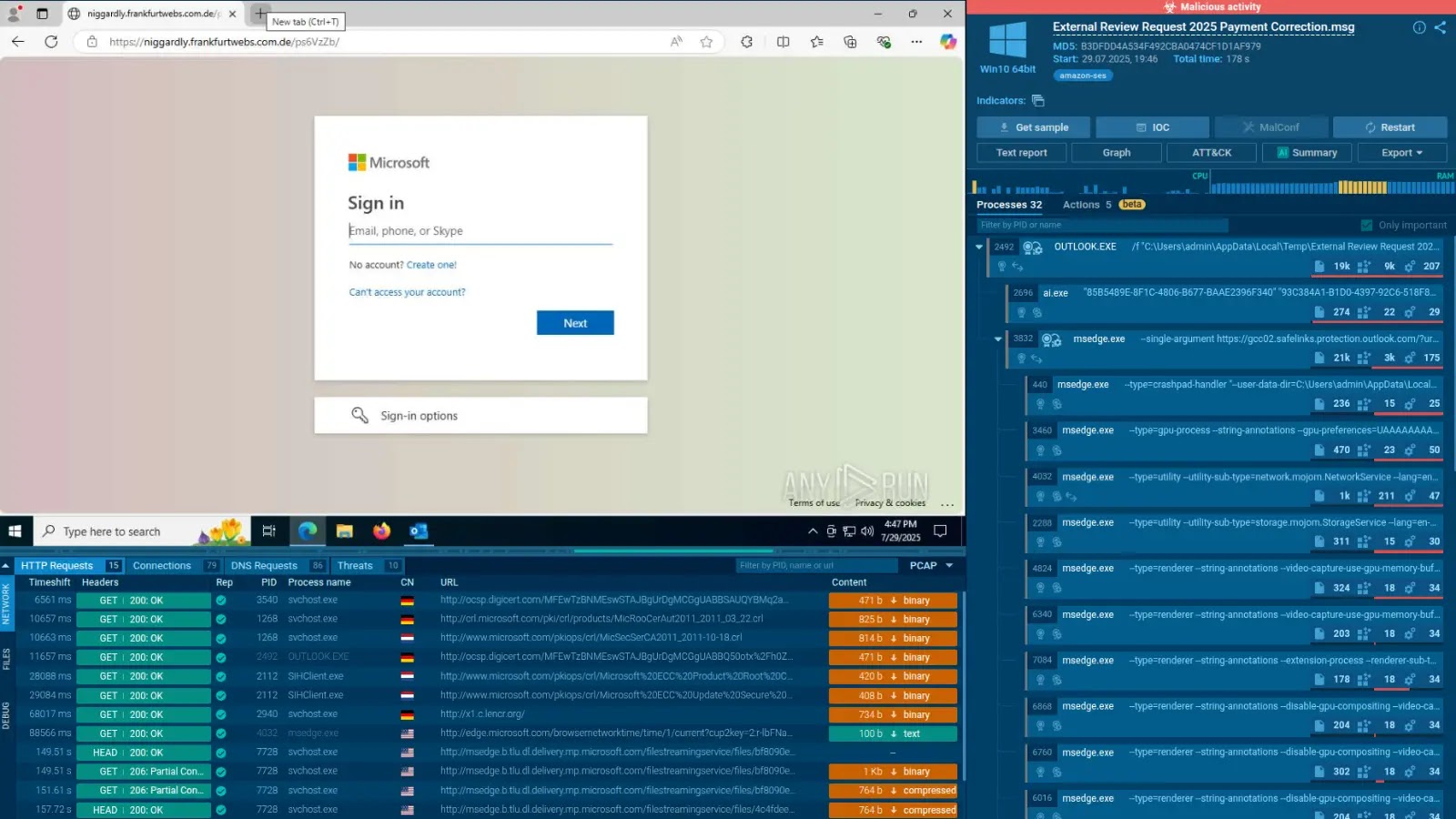
This campaign’s influence extends beyond individual users due to GitHub’s status as a trusted platform among developers, students, and security experts. The threat actor manipulated search results by adding unrelated SEO terms to repository descriptions, enhancing visibility and luring more unsuspecting victims. Data collected from compromised machines was silently transmitted to command-and-control servers, along with an information-stealing malware named StealC, designed to extract sensitive data.
Once a victim downloaded and extracted the ZIP file, a batch script initiated a LuaJIT interpreter to execute the obfuscated Lua script named SmartLoader. From the user’s perspective, the malware concealed its activity by using Windows API calls to hide the console window immediately after execution. SmartLoader performed anti-debug checks and used a blockchain dead drop resolver to locate its active command-and-control server, allowing operators to update infrastructure with ease.
Security Measures and Recommendations
Upon determining the active server, SmartLoader transmitted detailed host fingerprinting information and screenshots to a command-and-control server, which responded with encrypted instructions. Persistence was maintained through scheduled tasks that mimicked legitimate system activities. These tasks ensured the malware’s survival by periodically downloading fresh stages from GitHub, even if one path was obstructed.
To safeguard against such threats, security teams and users should verify the original sources of GitHub projects, monitor blockchain RPC endpoint connections, and be vigilant for batch-launched executables. Additionally, flagging multipart POST requests to bare IP addresses and enforcing application controls to prevent unsigned interpreters from executing can help mitigate risks.
For more updates, follow us on Google News, LinkedIn, and X. Set CSN as your preferred source on Google for instant updates.

.webp?ssl=1)