Hikvision, a number one supplier of surveillance and entry management techniques, faces critical safety dangers from two newly disclosed stack overflow vulnerabilities.
These flaws, tracked as CVE-2025-66176 and CVE-2025-66177, enable attackers on the identical native space community (LAN) to set off system malfunctions by sending specifically crafted packets. Each carry a excessive CVSS v3.1 base rating of 8.8, indicating vital potential impression with out requiring authentication.
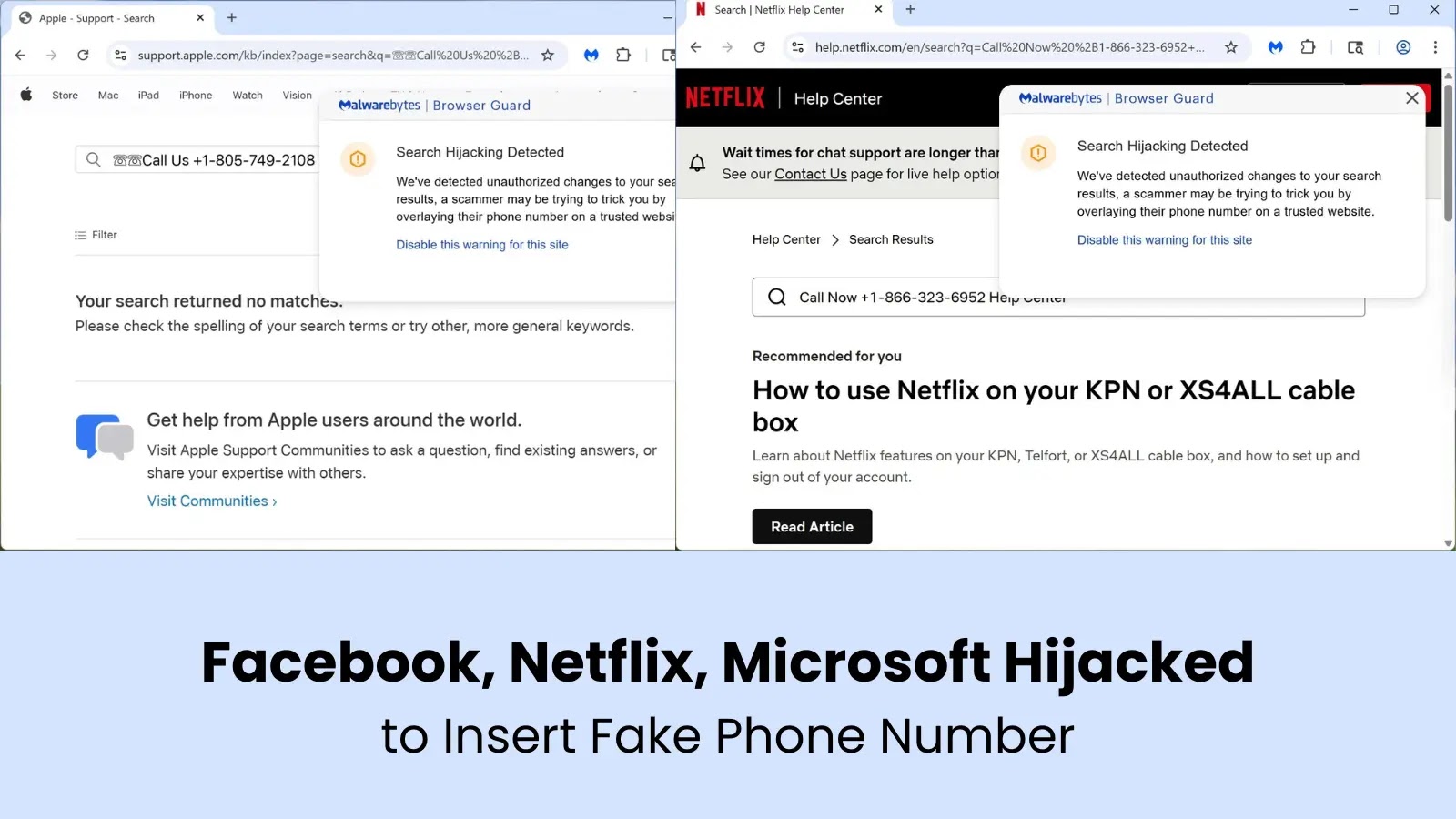
Safety researchers uncovered these points in Hikvision’s system Search and Discovery characteristic, a protocol used for community detection.
Exploitation calls for solely adjoining community entry, comparable to shared Wi-Fi or workplace LANs, making it a primary goal for insiders or opportunistic hackers. An unpatched system may crash completely, disrupting important operations in surveillance setups.
CVE IDAffected ProductsCVSS v3.1 Base ScoreDescriptionCVE-2025-66176Partial Entry Management Sequence Products8.8 (AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H)Stack overflow in Search and Discovery featureCVE-2025-66177Partial NVR, DVR, CVR, IPC Sequence Products8.8 (AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H)Stack overflow in Search and Discovery characteristic
The vector breakdown reveals low complexity: attackers want no privileges (PR:N) and no person interplay (UI:N), with excessive confidentiality, integrity, and availability impacts (C:H/I:H/A:H).
CVE-2025-66176 was reported by a Cisco Talos Workforce member, whereas CVE-2025-66177 got here from unbiased researchers Angel Lozano Alcazar and Pedro Guillen Nuñez. Their disclosures underscore ongoing scrutiny of IoT and surveillance gear, the place stack overflows have repeatedly enabled denial-of-service assaults.
Hikvision urges rapid patching. Customers can obtain firmware updates from the official assist web page. The corporate emphasizes community segmentation and disabling unused discovery options as interim mitigations.
These flaws arrive amid heightened issues over video surveillance safety. Final yr noticed comparable Hikvision advisories, prompting CISA alerts on provide chain dangers. Organizations counting on these gadgets, from good buildings to public security, ought to prioritize scans utilizing instruments like Nmap for uncovered providers.
Specialists warn that unpatched techniques may result in broader incidents, comparable to surveillance blackouts throughout emergencies. “LAN-adjacent assaults decrease the bar for disruption,” famous a Talos spokesperson. As threats evolve, distributors should speed up zero-trust implementations in embedded techniques.
Observe us on Google Information, LinkedIn, and X for every day cybersecurity updates. Contact us to characteristic your tales.


.webp?ssl=1)