A new remote access toolkit known as ‘CTRL’ has been linked to Russian hackers, who are utilizing it to hijack Remote Desktop Protocol (RDP) sessions and extract credentials from Windows systems. This toolkit, recently disclosed by Censys ARC, leverages a .NET framework to integrate various malicious tactics such as phishing, keylogging, reverse tunneling, and persistent access into a single attack sequence.
Discovery and Development
Researchers at Censys ARC identified the toolkit during a routine open directory scan, uncovering a malicious LNK file and multiple .NET payloads associated with the domain hui228[.]ru. This discovery suggests that the CTRL toolkit, not yet cataloged in public malware repositories or major threat intelligence sources, might be used privately rather than distributed widely.
The investigation revealed that the operation is likely orchestrated by a Russian-speaking developer, as evidenced by Russian-language strings and development artifacts. The toolkit appears to be actively maintained, targeting contemporary Windows systems, which implies ongoing development efforts.
Mechanics of the Attack
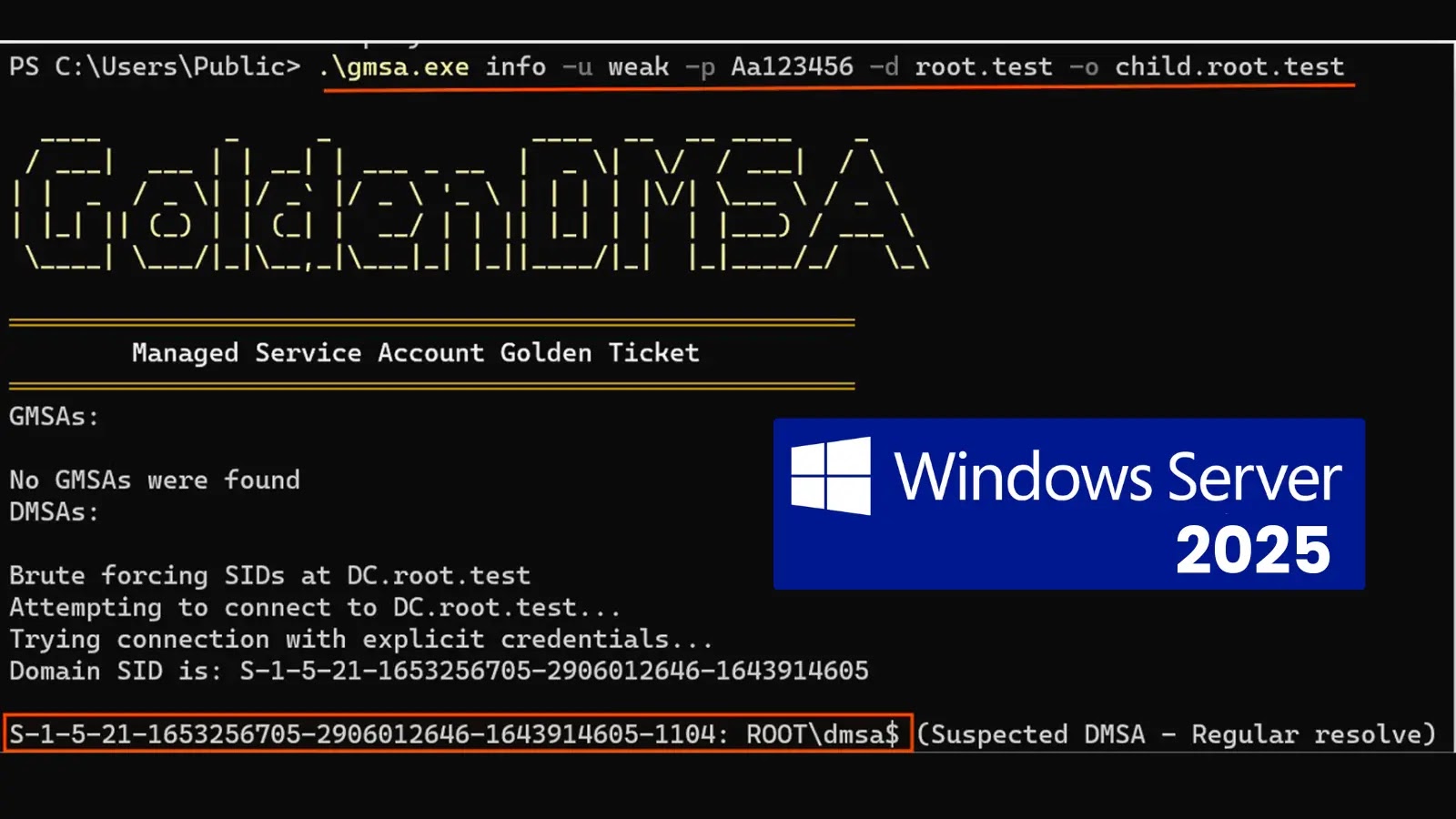
The attack sequence begins with a deceptive shortcut file masquerading as a private key archive. This LNK file executes concealed PowerShell commands that decode and initiate a multi-stage loader entirely in memory. The malware cleverly embeds payloads within Windows registry keys associated with Explorer, enabling them to blend seamlessly with legitimate system data.
Once operational, the malware establishes scheduled tasks, modifies firewall rules, and downloads further components to secure long-term access to the compromised system. It can bypass User Account Control through registry manipulation and a signed Microsoft binary, facilitating the installation of the complete toolkit that sustains access even after reboots.
RDP Hijacking and Network Evasion
The most concerning capability of the CTRL toolkit is its ability to enable concealed RDP access. By altering the termsrv.dll file and implementing RDP Wrapper, attackers can initiate simultaneous RDP sessions without the user’s knowledge. Furthermore, the toolkit includes a counterfeit Windows Hello PIN prompt that mimics the genuine interface, capturing the victim’s credentials.
In addition to these features, a background keylogger and command execution via a named pipe named ctrlPipe allow attackers to interact with the infected machine locally, minimizing the need for conspicuous command-and-control communication. The malware employs Fast Reverse Proxy (FRP) to establish reverse tunnels back to hacker-controlled infrastructure, circumventing typical detection methods associated with remote access trojans.
Indicators of Compromise and Defense
Key indicators of compromise include IP addresses 194.33.61.36 and 109.107.168.18, used for payload hosting and FRP relays, and the domain hui228[.]ru for command-and-control activities. Malicious registry entries and files such as C:Tempkeylog.txt and C:ProgramDatafrpfrpc.toml are used for storing keystrokes and FRP configurations.
Censys ARC advises monitoring for atypical binary data in Explorer registry keys, unexpected scheduled tasks, RDP Wrapper installations, and hidden administrator accounts. Additionally, defenders should be vigilant for outbound FRP traffic and anomalous connections to the identified infrastructure.