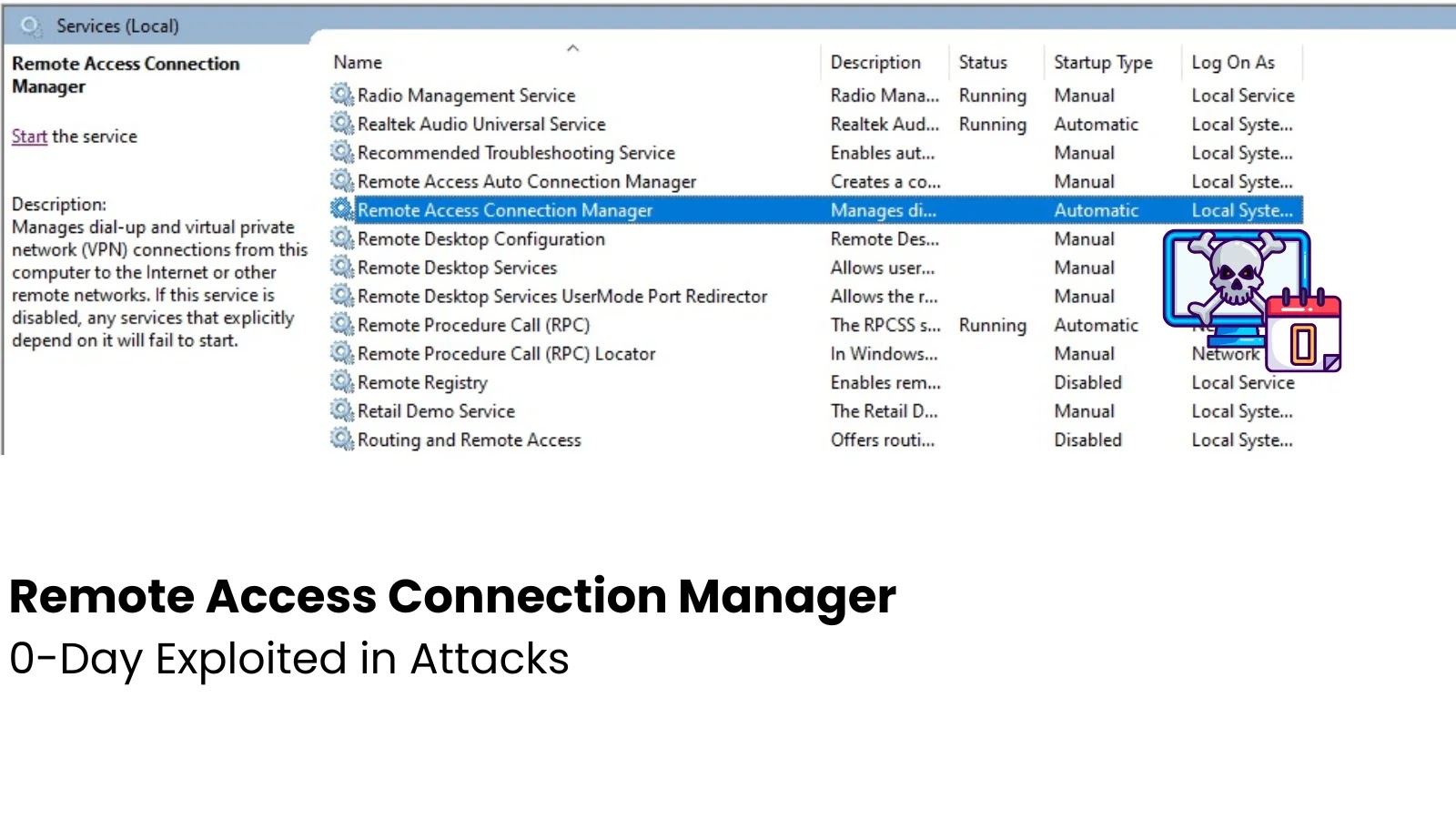
A recently uncovered vulnerability, known as PhantomRPC, in Windows Remote Procedure Call (RPC) architecture, poses a significant security risk across all Windows versions. This flaw allows attackers to escalate privileges to SYSTEM-level access, according to research shared by Kaspersky’s application security specialist Haidar Kabibo at Black Hat Asia 2026.
Unpatched Vulnerability Details
PhantomRPC is a design flaw rather than a typical memory corruption or logic issue. It targets the Windows RPC runtime’s handling of connection requests to inactive RPC servers. Specifically, when a high-privilege process attempts to connect with an offline server, the runtime fails to confirm the legitimacy of the responding server. This oversight allows attackers with control over low-privilege processes to deploy deceptive RPC servers, intercepting and manipulating communication.
Exploitation Techniques Identified
The vulnerability presents five distinct exploitation strategies, each unaddressed by Microsoft. One such method involves coercing the Group Policy Client service to inadvertently communicate with a malicious server, granting SYSTEM-level access. Another scenario arises when Microsoft Edge initiates an RPC call during startup, providing an opportunity for privilege escalation to Administrator levels.
Additional methods include exploiting the Diagnostic System Host’s periodic polling, manipulating ipconfig.exe’s interaction with the DHCP Client service, and taking advantage of the Windows Time service’s initial connection attempts. Each method leverages the same underlying flaw, exploiting the lack of server legitimacy verification.
Microsoft’s Response and Mitigation Strategies
Despite being reported to Microsoft Security Response Center in September 2025, the issue remains unpatched, classified as of moderate severity due to the prerequisite of SeImpersonatePrivilege. As no CVE has been assigned and no fix scheduled, organizations are advised to adopt interim protective measures.
Security experts recommend enabling ETW-based RPC monitoring to detect anomalies, activating disabled services to occupy legitimate endpoints, and restricting SeImpersonatePrivilege to processes that absolutely require it. Tools from the research have been made available by Kaspersky for organizations to audit their systems for potential exploit patterns.
For ongoing cybersecurity insights, follow us on Google News, LinkedIn, and X. Contact us to share your cybersecurity stories.