A financially driven, Russian-speaking cybercriminal has used commercial AI tools to infiltrate over 600 FortiGate devices across 55 nations, according to Amazon Threat Intelligence. This activity occurred between January 11 and February 18, 2026, highlighting a growing trend of AI-assisted cybercrime.
Exploiting Security Gaps
The threat actor bypassed FortiGate vulnerabilities by capitalizing on exposed management ports and weak, single-factor authentication credentials. These fundamental security weaknesses allowed an unsophisticated individual to exploit them on a large scale, as confirmed by CJ Moses, Amazon’s Chief Information Security Officer.
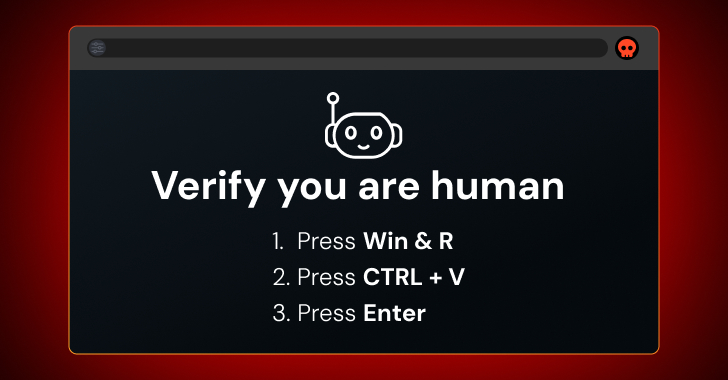
Although the cybercriminal lacked advanced technical skills, they overcame this limitation using commercial AI tools to aid in various attack stages. These tools facilitated tool development, attack planning, and command generation, enabling the actor to execute complex operations they otherwise couldn’t.
AI’s Role in Cybercrime
The primary AI tool operated as the main driver of the operation, with a secondary tool serving as backup. This dual-tool approach allowed the attackers to pivot within compromised networks. Despite not being linked to state-sponsored groups, the actor leveraged AI to scale their operations, a trend increasingly noted by cybersecurity experts.
Amazon’s investigation revealed that the actor breached multiple organizations’ Active Directory environments, extracted credential databases, and targeted backup infrastructures, hinting at potential ransomware attacks. The adaptability and scalability offered by AI are lowering the entry barriers for such cybercrimes.
Mitigation and Future Outlook
Amazon identified the attackers’ infrastructure, which hosted AI-generated plans and custom tools, characterizing it as an “AI-powered assembly line for cybercrime.” The attacks involved scanning FortiGate management interfaces across various ports and using common credentials to gain unauthorized access.
The compromised devices were found in diverse regions, including South Asia, Latin America, and Northern Europe. Following network access, the actor deployed reconnaissance tools with AI-assisted code, indicative of their reliance on automated solutions to compensate for limited skills.
Organizations must bolster their defenses by securing management interfaces, changing default credentials, implementing multi-factor authentication, and isolating backup servers. As AI-driven threats rise in 2026, maintaining robust security practices will be crucial in countering both skilled and novice cybercriminals.