Nov 26, 2025The Hacker NewsSoftware Safety / Patch Administration
If you happen to’re utilizing neighborhood instruments like Chocolatey or Winget to maintain techniques up to date, you are not alone. These platforms are quick, versatile, and simple to work with—making them favorites for IT groups. However there is a catch…
The very instruments that make your job simpler may also be the rationale your techniques are in danger.
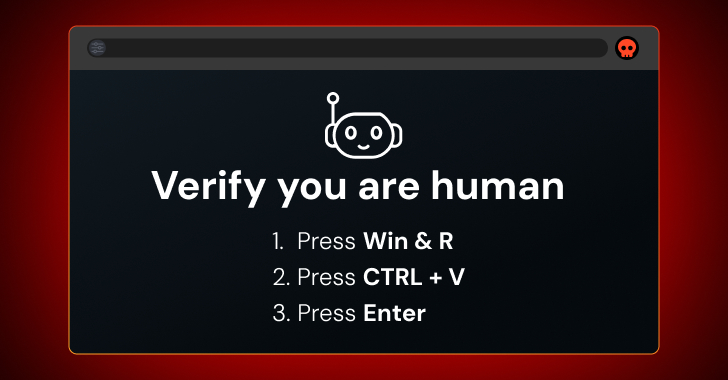
These instruments are run by the neighborhood. Which means anybody can add or replace packages. Some packages could also be previous, lacking security checks, or modified by mistake or on function. Hackers search for these weak spots. This has already occurred in locations like NPM and PyPI. The identical dangers can occur with Home windows instruments too.
That can assist you patch safely with out slowing down, there is a free webinar arising. It is led by Gene Moody, Subject CTO at Action1. He’ll stroll via how these instruments work, the place the dangers are, and the best way to defend your techniques whereas protecting updates on observe.
On this session, he’ll check how secure these instruments actually are. You may get sensible steps you should utilize immediately—nothing theoretical, simply what works.
The aim is to not scare you away from neighborhood instruments. They’re helpful. However they want guardrails—guidelines that make it easier to use them safely with out slowing you down.
You’ll study:
🔒 How one can spot hidden dangers
⚙️ How one can set security checks like supply pinning, allow-lists, and hash/signature verification
📊 How one can prioritize updates utilizing identified vulnerability knowledge (KEV)
📦 How to decide on between neighborhood instruments, direct vendor sources, or a mixture of each
If you happen to’re undecided when to make use of neighborhood repos and when to go straight to the seller, this session will make it easier to determine. You may additionally see the best way to combine each in a secure manner.
This webinar is for anybody who manages software program updates—whether or not you are on a small crew or a big one. If you happen to’ve ever questioned what’s actually inside that subsequent patch, this session is for you.
It is free to attend, and you will depart with clear actions you may apply the identical day. Save your spot right here.
Discovered this text attention-grabbing? This text is a contributed piece from one among our valued companions. Observe us on Google Information, Twitter and LinkedIn to learn extra unique content material we submit.