In a recent software supply chain attack, cybercriminals have infiltrated the widely-used Python package, Lightning, introducing malicious versions to facilitate credential theft. Security firms Aikido Security, OX Security, Socket, and StepSecurity have identified versions 2.6.2 and 2.6.3, released on April 30, 2026, as the compromised versions. These developments are seen as a continuation of the Mini Shai-Hulud campaign, previously targeting SAP-related npm packages.
Details of the PyTorch Lightning Attack
The Python Package Index (PyPI) repository administrators have quarantined the affected project. PyTorch Lightning is an open-source Python framework known for its high-level interface for PyTorch, boasting over 31,100 stars on GitHub. According to Socket, the compromised versions contain a concealed _runtime directory housing a downloader and an obfuscated JavaScript payload. This payload automatically activates upon importing the Lightning module, requiring no further user interaction.
The attack sequence initiates with a Python script (‘start.py’) that downloads and runs the Bun JavaScript runtime. This setup then executes an 11MB obfuscated payload (‘router_runtime.js’), designed to steal credentials extensively. Project maintainers have acknowledged awareness of the issue and are investigating its origins, with initial signs pointing to a possible GitHub account compromise.
Implications and Recommended Actions
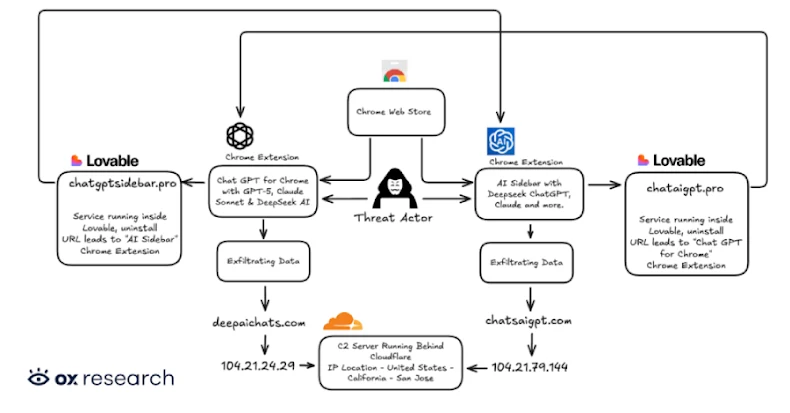
The stolen credentials include GitHub tokens, which are verified against the ‘api.github[.]com/user’ endpoint before being used to inject malicious payloads into repositories. These operations create new files or overwrite existing ones without pre-checks, using a hardcoded identity to mimic Anthropic’s Claude Code.
Moreover, the malware exploits an npm-based propagation strategy, modifying local npm packages with a postinstall hook in the ‘package.json’ file. This alteration invokes the malicious payload, updates the version number, and repacks the .tgz tarballs. Developers who unknowingly publish these tampered packages risk spreading the malware across user systems.
Connection to TeamPCP and Further Exploits
As a precaution, developers should block versions 2.6.2 and 2.6.3 of Lightning, remove them if installed, revert to version 2.6.1, and rotate any exposed credentials. This attack is attributed to TeamPCP, a threat actor with a history of similar exploits, now operating a website on the dark web after their account suspension from X.
In a related incident, the intercom-client version 7.0.4 has also been compromised under the Mini Shai-Hulud campaign, using a similar approach as the SAP packages to deploy credential-stealing malware. This connection is notable due to shared technical details, including payload characteristics and credential harvesting methods, linking it to previous attacks involving Checkmarx, Bitwarden, and others.
These incidents underscore the importance of vigilance in software supply chains, highlighting the need for robust security measures and prompt responses to emerging threats.