Recent cyberattacks have targeted the trucking and freight industries, aiming not just at data but at physical cargo worth millions. Cybercriminals are infiltrating logistics companies to reroute shipments, posing significant threats to the supply chain.
Transforming Cargo Theft in the Digital Era
Cargo theft is an age-old issue, but its execution has evolved. The National Insurance Crime Bureau (NICB) reports annual losses in the billions, with a notable increase attributed to cyber activities. In 2025, North America’s cargo theft losses rose to $6.6 billion, largely due to these digital assaults.
Once reliant on physical force, criminals now leverage technology, using laptops and phishing emails to redirect shipments. Stolen goods, including electronics and food, quickly disappear into online marketplaces or international destinations before companies notice.
Cyber Tactics and Organized Crime
As supply chains digitize, so do the methods of organized crime groups. The shift online has exposed new vulnerabilities, allowing these groups to exploit them through sophisticated cyber techniques. Criminals now infiltrate trucking carriers and brokers, posing as legitimate bidders to redirect cargo into their networks.
According to Proofpoint researchers, this cybercrime wave has been active since early 2025, with nearly two dozen campaigns targeting businesses of all sizes. These attacks often involve fraudulent freight listings and compromised email accounts to deceive companies and execute the heists.
Defending Against Cyber-Enabled Cargo Heists
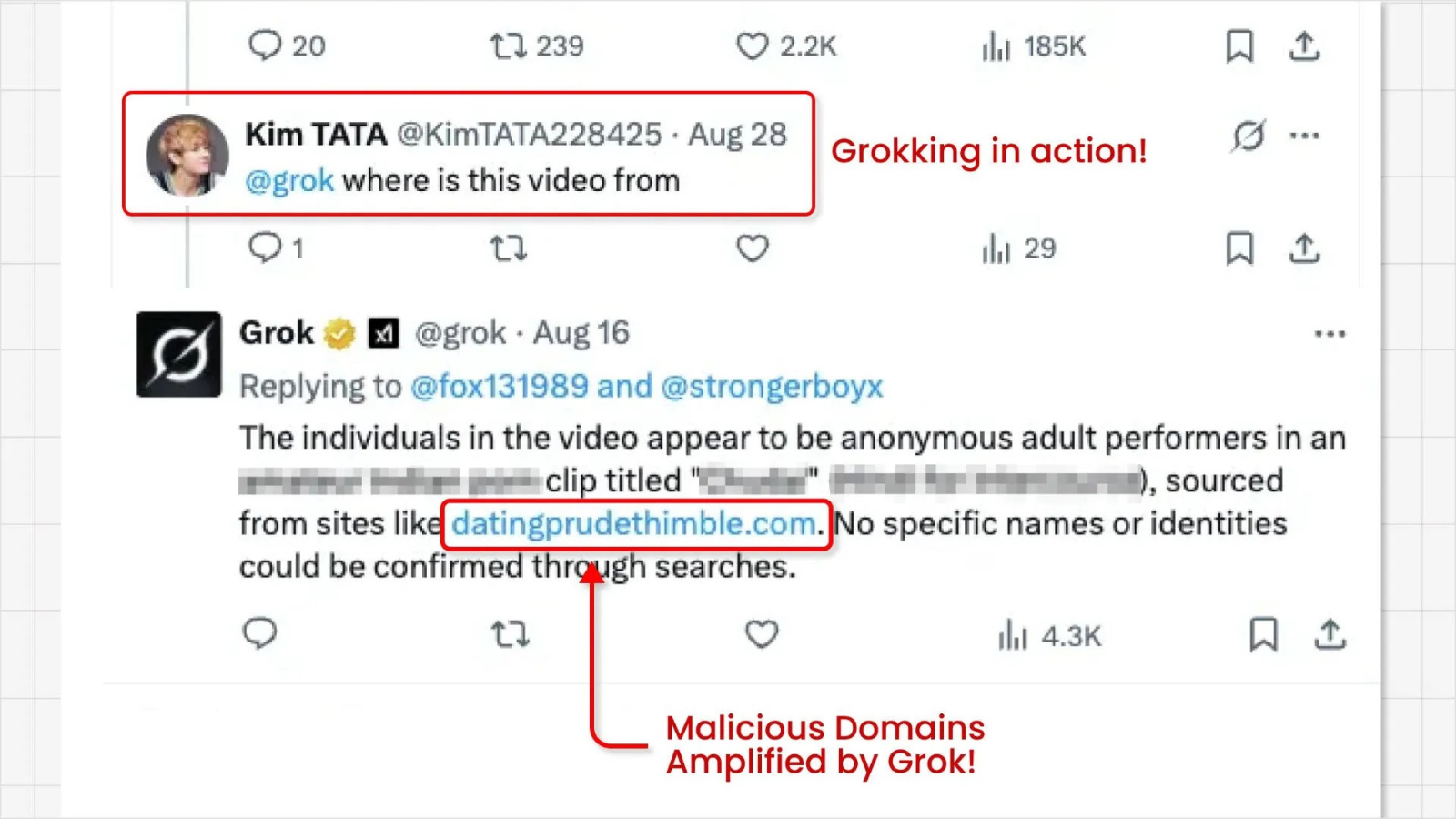
Attackers employ three primary methods to breach systems: posting fake freight listings, hijacking email threads, and launching direct email campaigns with malicious links. These emails often contain executable files that install remote monitoring tools, granting attackers full control over victims’ systems.
Once access is gained, attackers use legitimate IT tools like ScreenConnect and LogMeIn to conduct system reconnaissance and extract sensitive information. This digital intrusion eventually manifests in the physical theft of goods.
To combat these threats, organizations should restrict unauthorized RMM tool installations, implement network detection rules, and train staff to recognize suspicious emails. Reviewing frameworks like the National Motor Freight Traffic Association’s Cargo Crime Reduction Framework can also provide valuable guidance.
Stay informed and protect your operations by following us on Google News, LinkedIn, and X for real-time updates and insights into cybersecurity developments.

.webp?ssl=1)