A newly discovered cyber threat group, identified as UNC6692, has been orchestrating a complex multi-layered intrusion campaign targeting enterprise networks. This group cleverly abuses Microsoft Teams by posing as IT helpdesk staff to infiltrate organizations without exploiting software vulnerabilities.
Exposing the UNC6692 Campaign
On April 22, 2026, the Google Threat Intelligence Group and Mandiant researchers unveiled the methods of UNC6692. The group exploits trusted enterprise tools to gain deep access to networks, bypassing traditional security measures. The campaign began in December 2025 with a strategic email bombing, overwhelming victims and paving the way for a direct attack via Microsoft Teams.
Hackers impersonated IT staff, sending phishing messages through Teams to convince employees to download malicious software. Microsoft reported that these attacks misuse legitimate external collaboration features, tricking users into ignoring security warnings.
Intricate Infection Process
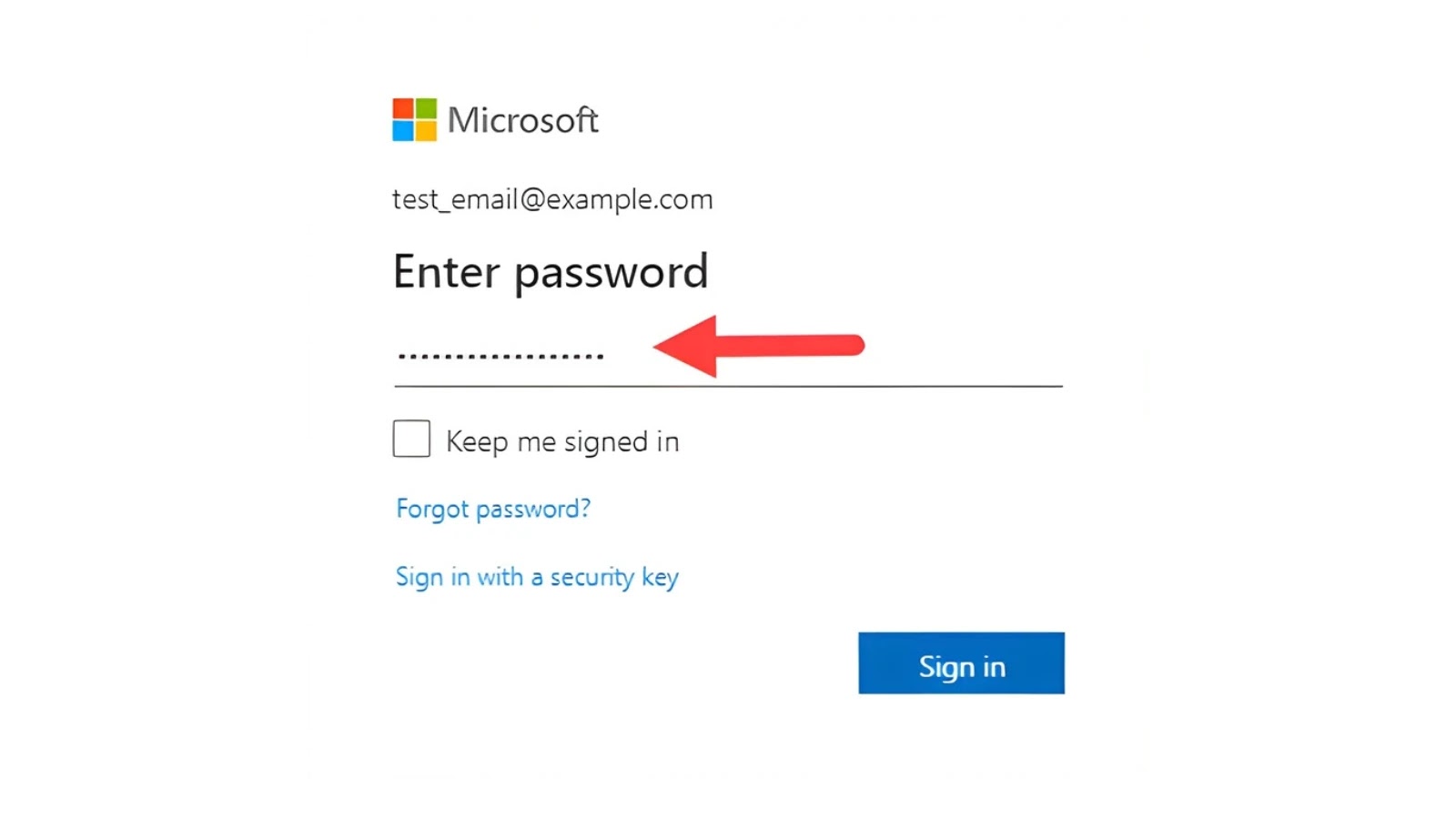
The attack unfolded in stages, beginning with a deceptive link in a Teams message, leading to a phishing page that mimicked a utility tool. This page initiated a multi-phase attack pipeline designed to capture credentials and deploy malware.
In the initial phase, victims were redirected to Microsoft Edge to maximize exploit effectiveness. Subsequent steps involved credential harvesting using fake prompts, and distraction techniques masked ongoing data theft. Malware was then installed, creating an initial foothold for further network compromise.
The SNOW Malware Framework
UNC6692 employs the SNOW ecosystem, a modular malware suite. It includes SNOWBELT, a browser extension for command and control operations; SNOWGLAZE, a tunneling tool routing traffic through victims; and SNOWBASIN, a server tool for executing commands and capturing data.
These tools allow the attackers to scan networks, extract sensitive data, and gain administrative access without detection. By exploiting cloud services like AWS and Heroku, the campaign’s traffic blends into normal encrypted web traffic, evading traditional security filters.
Implications and Preventive Measures
UNC6692’s use of trusted cloud services highlights the need for enhanced monitoring beyond standard process checks. Organizations should scrutinize browser extensions and cloud egress activities while controlling external access to Microsoft Teams.
As demonstrated, the reliance on employee trust in familiar platforms can be a critical vulnerability. Strengthening awareness and monitoring can mitigate the risks posed by such sophisticated threats.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Stay informed and secure to protect your organization from emerging threats.