A sophisticated variant of the ClickFix attack technique is now targeting Windows users, utilizing rundll32.exe and WebDAV to bypass common security measures. This new approach deviates from older methods that relied on PowerShell or mshta, enhancing its ability to evade detection.
Innovative Attack Methods
Unlike previous versions, this variant leverages two integral Windows components, rundll32.exe and WebDAV, to discreetly deliver malicious payloads. This tactic evades many traditional security alerts, posing a greater threat, especially to organizations focused on script-based threat detection.
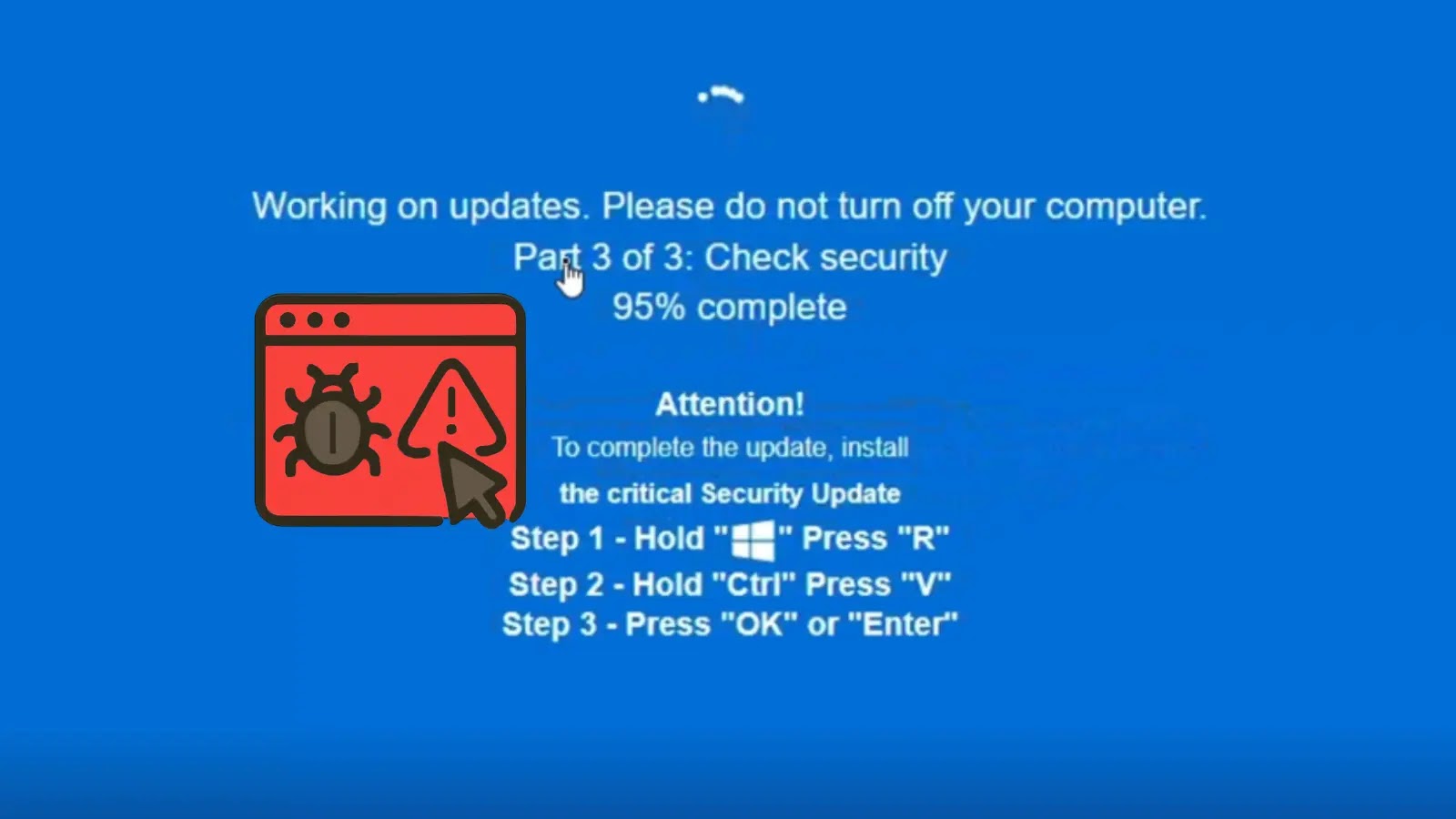
ClickFix attacks typically deceive users into executing harmful commands. In this instance, attackers masquerade a phishing website as a CAPTCHA verification page, persuading users to execute commands via the Windows Run dialog. The site, identified as “healthybyhillary[.]com,” misleads visitors into executing scripts that appear innocuous.
Detection Evasion Tactics
CyberProof analysts discovered this ClickFix variant during threat assessments, noting its reduced reliance on scripting engines. By using rundll32.exe with WebDAV, the attack accesses remote files over HTTP, loading malware from an attacker-controlled server. This method adds complexity, making it harder for security teams to identify the attack early.
The malware operates largely in memory, transitioning to PowerShell at a later stage. This later phase utilizes Invoke-Expression (IEX) to download further payloads without leaving a trace on disk, employing PowerShell flags to minimize noise.
Advanced Obfuscation Techniques
The core payload, SkimokKeep, is a secondary loader using advanced techniques to evade detection. Delivered as a Windows DLL, it avoids typical Windows API imports, instead employing a DJB2-style hashing algorithm to obscure its operations. This strategy complicates static analysis efforts.
To further evade detection, the malware checks for sandbox and virtual environments, employing anti-debugging measures. It also injects code into trusted processes like chrome.exe and msedge.exe, maintaining access while concealing its presence.
Security teams should monitor rundll32.exe executions involving davclnt.dll and DavSetCookie to identify WebDAV-based payload deliveries. Command-line auditing of LOLBins and restricting or monitoring WebDAV traffic is recommended. Blocking connections to known malicious IPs and domains, alongside enhancing user awareness about fake CAPTCHA threats, can fortify defenses.
For more updates, follow us on Google News, LinkedIn, and X. Set CSN as a preferred source in Google for instant updates.