Cybersecurity experts have recently identified a new malware threat named Speagle, which leverages the existing capabilities of Cobra DocGuard, a legitimate document security application. This malware is engineered to clandestinely collect confidential data from compromised systems and send it to a server associated with Cobra DocGuard, which attackers have overrun. The operation is disguised as routine communication between the client and server, according to a joint report by Symantec and Carbon Black.
Background on Cobra DocGuard
Cobra DocGuard, developed by EsafeNet, is a platform focused on document protection and encryption. Its misuse in cyberattacks has been documented on two occasions prior to the current situation. In one notable case, a gambling firm in Hong Kong was attacked in September 2022 through a malicious update of the software, as reported by ESET in January 2023.
In August of the same year, Symantec highlighted a new threat group named Carderbee, which exploited a trojanized version of Cobra DocGuard to deploy PlugX, a backdoor favored by Chinese cybercriminal groups such as Mustang Panda. The attacks affected various organizations across Hong Kong and other parts of Asia.
Characteristics and Implications of Speagle Malware
The identity of the perpetrators behind Speagle remains unknown. This malware is particularly noteworthy because it targets systems with Cobra DocGuard installed, suggesting a focused approach likely intended for intelligence gathering or industrial espionage. Broadcom’s threat analysis teams have labeled this activity Runningcrab and speculate that it could either be the work of a state-sponsored group or a private contractor available for hire.
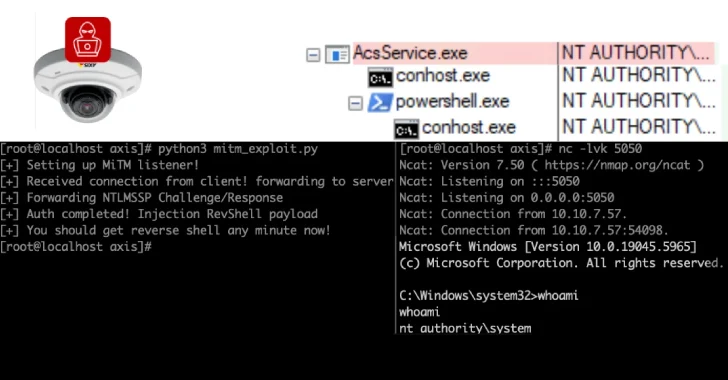
The method of Speagle’s delivery to its victims is not yet clear, though it is suspected to involve a supply chain attack, similar to previous incidents. The use of Cobra DocGuard’s infrastructure as a command-and-control point, as well as a data exfiltration portal, plays a critical role in Speagle’s operations.
Technical Details and Future Outlook
Once the 32-bit .NET executable is initiated, it checks for the Cobra DocGuard installation folder and proceeds to systematically collect and transmit data from the infected system. This includes system details and specific files like web browser history and autofill data. Additionally, a variant of Speagle can toggle certain data collection types and search for files linked to Chinese ballistic missiles such as the Dongfeng-27.
Speagle represents a sophisticated threat that cleverly manipulates Cobra DocGuard’s client to conceal its malicious actions and uses its infrastructure to obfuscate data exfiltration activities. Researchers suggest that its developers might have been inspired by previous supply chain attacks involving the software, choosing it for its vulnerabilities and widespread use among targeted entities.